Adversarial Exposure Validation for OT/ICS
OT/ICS can't be tested like IT. We've designed for this.
Every other security validation tool was designed for enterprise IT — then retrofitted for OT. SCYTHE was designed from the ground up for environments where uptime and safety are non-negotiable.
The Core Challenge
OT/ICS security testing has four constraints IT testing simply doesn't.
Understanding these constraints is why most IT-focused security tools fail in industrial environments — and why SCYTHE was built differently.
Active Threat Landscape
The adversaries targeting your environment use OT-specific techniques. So should your testing.
SCYTHE maps emulation campaigns to the real actors targeting critical infrastructure, so you're testing the playbook they're actually running.
STATE
Chinese state-nexus group conducting long-duration espionage and pre-positioning against U.S. electric utilities, telecommunications, and defense. Specializes in living-off-the-land to avoid detection with demonstrated interest in OT network diagrams and operational data.
STATE
Responsible for the most destructive cyberattacks on industrial infrastructure in history — 2015 and 2016 Ukrainian power grid attacks and Industroyer/Industroyer2 malware designed to directly interact with ICS protocols. Remains the most capable threat to EU and NA energy.
PETROCHEM
Deployed TRITON malware against Safety Instrumented Systems (SIS) in Middle Eastern petrochemical facilities — targeting the safety systems designed to prevent catastrophic accidents. First known malware specifically designed to cause physical harm to humans.
FROM THE PRACTITIONER COMMUNITY
See how a real CTI program operationalizes the exact intelligence above into tested defenses.
This is exactly where SCYTHE accelerates CTI operationalization, translating active threat actor intelligence into tested, validated defenses before an incident proves the gap for you.
“I believe we should be testing in our production OT environments. I can't say that enough. They are different than our labs. We can't build a lab that looks like our production environment, especially at scale.”
|
AW
|
Alex Waikas OT Security Engineer, Southern Company |
HOW SCYTHE OPERATES IN OT/ICS ENVIRONMENTS
Five principles convention tools
can't offer.
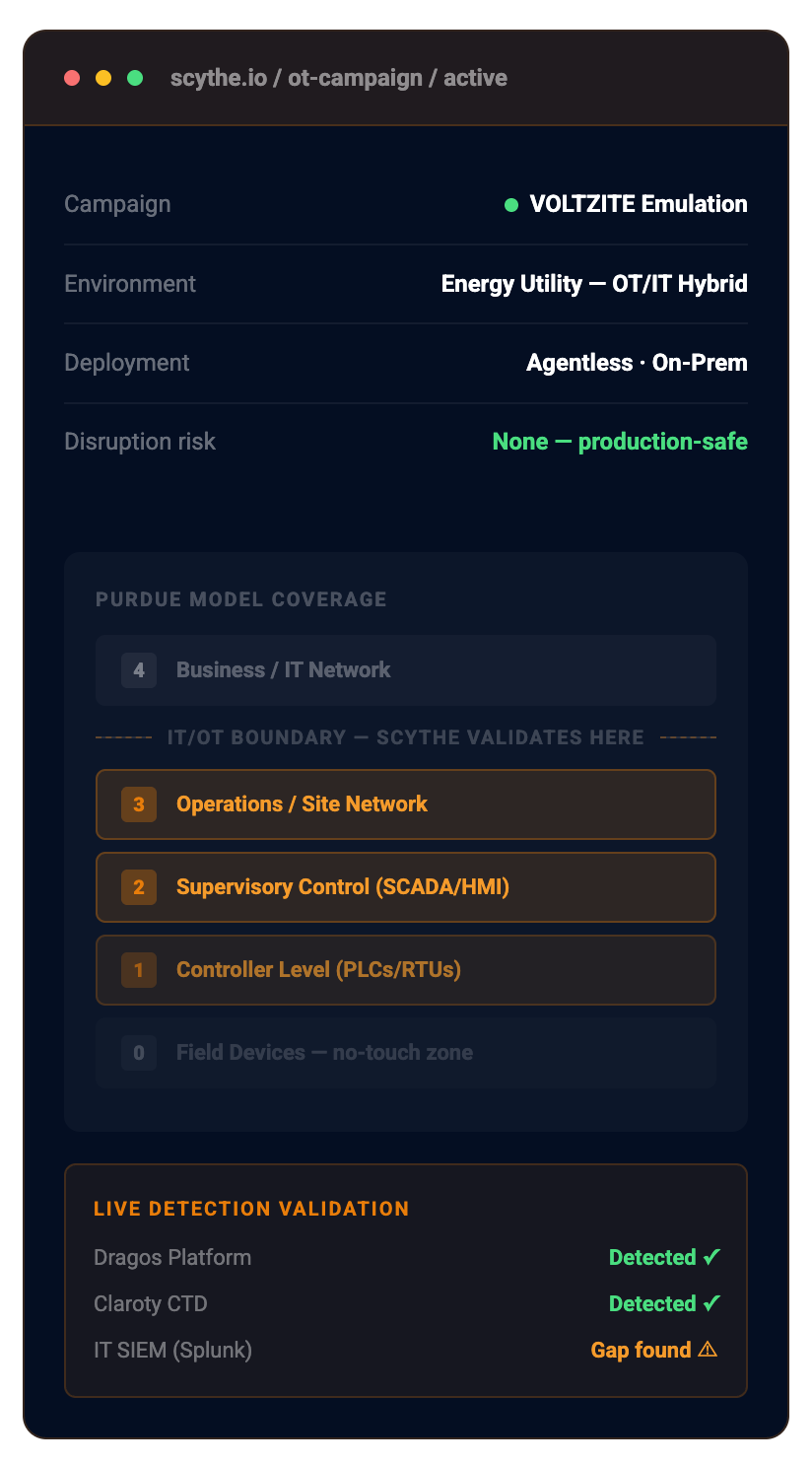
SCYTHE is purpose-built to operate across the IT/OT boundary, validating attack
paths that matter most without disrupting the operations you're protecting.
|
|||||
|
|||||
|
|||||
|
|||||
|
Measured Benefits
What OT operators achieve with SCYTHE.
Continuous validation turns assumed OT coverage into defensible, auditable proof. Based on customer-reported outcomes from critical infrastructure operators.
"SCYTHE improves our security control efficacy, optimizing budget spend and ROI, while also enhancing talent development, training, and partner relationships.
Regulatory Alignment
Built for the frameworks that govern critical infrastructure security.
Continuous adversary emulation with SCYTHE produces the defensible, repeatable evidence record that regulators require — not a point-in-time PDF.
CIP
62443
CSF
SD
Common Questions
Questions OT security teams ask first.
These are the questions every critical infrastructure defender asks before testing in a live OT environment.
Prove your OT defenses work, without disrupting operations.