Adversarial Exposure Validation Platform
Prove your defenses work.
Before attackers do.
Continuous adversarial emulation across IT, cloud, and OT — so you know exactly what your controls catch, and what they don't.
SCYTHE runs real MITRE ATT&CK-mapped campaigns in your actual environment on a continuous schedule — validating detection, alerting, and response against the threat actors targeting your industry right now.
TRUSTED BY
why scythe platform vs. more of the same
The tools you already own aren't the problem. Not knowing if they are working is.
Your EDR vendor validates their product in their lab. SCYTHE validates it in yours — against the techniques being used against your industry, right now. Those are different tests with different answers.
| Instead of assuming… | SCYTHE proves… |
|---|---|
| Your EDR catches credential dumping | Whether T1003.001 fires in your specific config and environment |
| Your SIEM rules are correctly tuned | Which rules generate actionable alerts vs. noise or silence |
| Your annual pen test reflects current risk | What your controls catch against techniques active in your industry today |
| Your SOC would catch lateral movement | Exactly how long detection takes — and where the chain breaks |
|
That's not a new investment. It's proof that your current investments are working — or the evidence you need to fix them before an attacker finds out first.
|
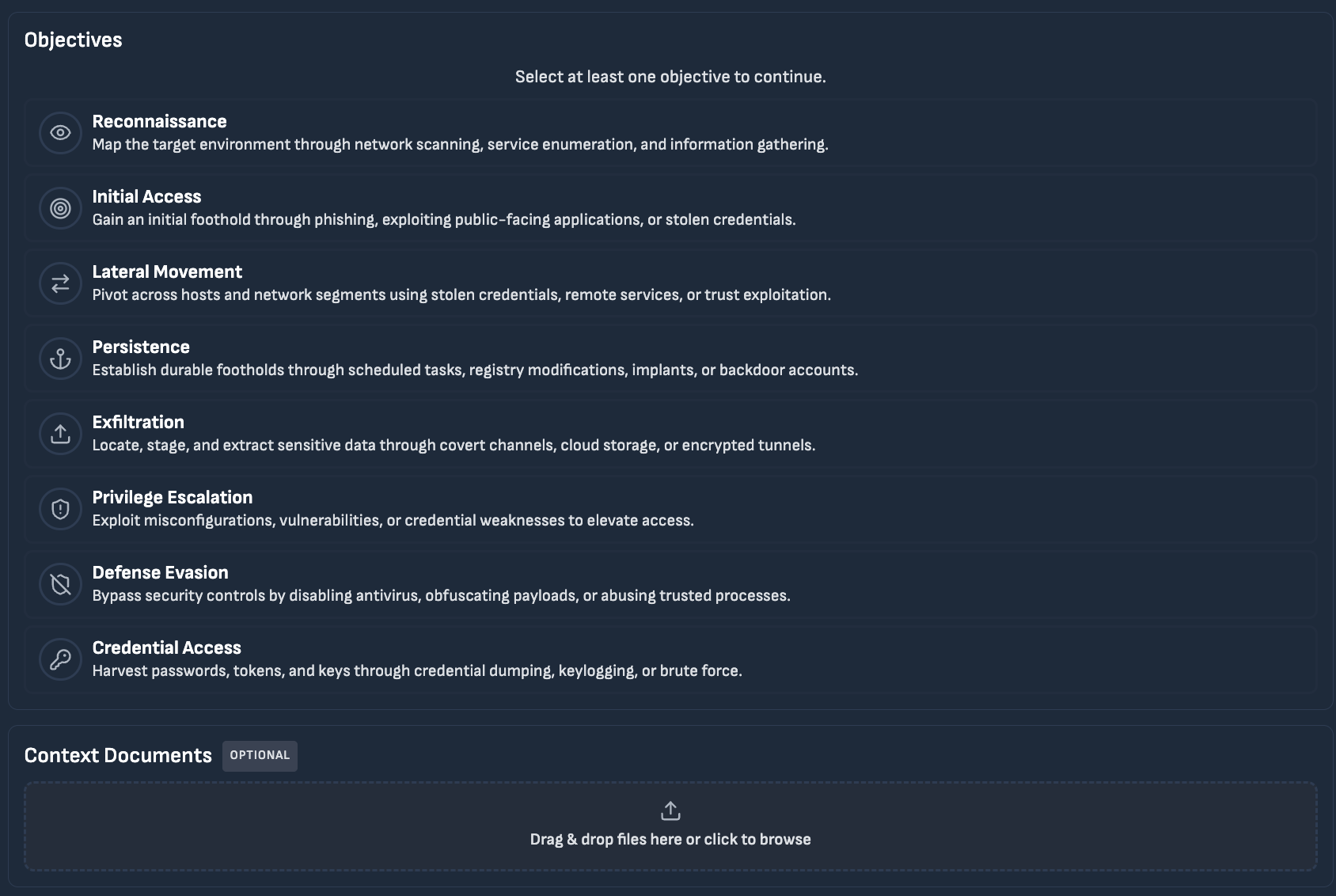
PLATFORM CAPABILITIES
Four capabilities. One continuous program.
Each capability is production-safe, fully auditable, and continuously updated with new adversary techniques as the threat landscape evolves.
Adversarial emulation AI-powered test generation Control validation Detection engineering
Emulate real adversaries, not generic scripts
SCYTHE's campaign library emulates named threat actors mapped to MITRE ATT&CK, from initial access through lateral movement to objectives. Every technique runs in your actual environment against your real controls, not in a sandbox.
Multi-stage attack chains, evasion behaviors, and living-off-the-land techniques are all supported. Campaigns can be scheduled, change-triggered, or run on demand.
Named threat actor emulation Full kill-chain campaigns MITRE aligned Production-safe Multi-stage chains
Measured Outcomes
What customers see after deploying SCYTHE.
Continuous validation turns assumptions into evidence. Based on customer-reported outcomes.
"SCYTHE has cut our MITRE ATT&CK testing from days to just moments."
John Strand — Black Hills Information Security
See It In Action
What the platform looks like when it's running.
Five views your team will live in. Each one turns a question that used to take weeks into an answer you have continuously.
01 Dashboard
The AEV Dashboard — operator-first view of defense posture, control efficacy, risk scores, and tactic hotspots. All metrics update continuously as campaigns execute.
Defense posture gauges
Four dials showing logged, alerted, blocked, and defended outcomes across all 465 events. At a glance you see exactly where the response chain is breaking down.
Mean TTD & TTTE — rated
60h 24m to detect and 26h 20m to engage, both flagged POOR. These are the numbers that determine whether your team catches an attacker before damage is done.
Threat scenario scores
Ransomware 13/100, Phishing 17/100, Insider Threat 12/100 — scenario-specific scores show which threat categories your controls are least prepared for.
ATT&CK tactic hotspots
Execution accounts for 52 of 58 total issues. That's where to focus detection engineering first — not a guess, a measurement.
02 ATT&CK coverage heatmap
Live ATT&CK heatmap — updates automatically as campaigns execute. Gaps surface in real time, not at the end of a quarterly review.
Live coverage score
68% of tested ATT&CK techniques validated — updates in real time as each campaign completes.
Gap count — always current
14 techniques flagged as untested or failing. Each links to the specific technique, tactic, and affected control.
Tactic-level breakdown
Coverage shown by ATT&CK tactic row — see at a glance whether lateral movement or defense evasion is your weakest area.
Partial coverage flagged separately
Light blue means the EDR fired but the SIEM alert didn't generate — gaps that only show up when you test the full chain.
03 Campaign builder
Campaign generated from a plain-language threat description in under 60 seconds. Human approval required before anything executes.
Plain language input
Paste a CISA advisory, ISAC bulletin, or describe the scenario. SCYTHE extracts and maps TTPs automatically.
ATT&CK mapping — automatic
Every technique tagged with its ATT&CK ID and tactic. No manual mapping required.
Human approval gate
Nothing runs without explicit sign-off. AI builds the campaign — your team decides when and where it executes.
Full edit control
Add, remove, or reorder techniques before approving. The AI suggestion is a starting point, not a locked plan.
04 Validation results
Technique-level results showing exactly which controls fired, where the chain broke, and auto-created remediation tickets.
Detected / missed / partial
The three-number summary tells the story immediately. No hunting through logs to understand what happened.
Where in the chain it broke
"SIEM GAP" means the EDR fired but the alert didn't generate. Precision here determines whether the right team fixes the right thing.
"Full chain" is the standard
EDR detected, SIEM alerted, SOC workflow triggered. That's what passing looks like. Anything less is a gap.
Automatic ticket creation
Gaps create Jira or ServiceNow tickets instantly — pre-populated with technique context and remediation guidance.
05 Purple team exercise
Purple team exercise — red and blue teams share a live view of every technique, every detection outcome, and every rule tuned in real time. Coverage improves during the session, not after.
Shared operating picture
Red and blue teams see the same log simultaneously. No post-exercise debrief — both sides see outcomes in real time.
Rule tuning happens in-session
"TUNING" means the blue team updated the SIEM rule and queued a re-test before moving on. Gaps get fixed during the session, not three weeks later.
Coverage delta — measured live
54% coverage at the start, 68% by the end. Leadership can see the program improving in real time, not in a quarterly report.
Every session builds the program
Results feed into the cumulative ATT&CK heatmap. Each exercise is a permanent improvement to your detection library.
Ready to see what your controls actually catch?
Deployments & Integrations
Fits your environment. Integrates with your stack.
Integrations include:
EDR
 CrowdStrike Falcon
CrowdStrike Falcon  Microsoft Defender
Microsoft Defender  SentinelOne
SentinelOne  Cortex XDR
Cortex XDR SIEM
 Splunk
Splunk  Microsoft Sentinel
Microsoft Sentinel  IBM QRadar
IBM QRadar  Google Chronicle
Google Chronicle ITSM + more
 Elastic SIEM
Elastic SIEM  ServiceNow
ServiceNow  Jira
Jira COMMON QUESTIONS
What buyers typically ask.
We already have CrowdStrike and Splunk. Why do we need SCYTHE?
Buying a tool and validating a tool are different investments. CrowdStrike and Splunk are excellent at what they do. SCYTHE answers the question those tools can't answer for you: in your environment, against the specific techniques targeting your industry, does your detection chain actually work end to end?
The EDR fires, but does it generate a usable SIEM alert? Does that alert trigger the right SOC workflow? Does a ticket get created and assigned? Those questions require a platform that sits above and across your stack, not inside a single tool. That's what SCYTHE does.
How is this different from our annual penetration test?
Penetration tests find vulnerabilities. SCYTHE validates controls. Those are different questions.
A pen test tells you where an attacker could get in. SCYTHE tells you whether your detections would catch them if they did, and whether that's still true after your environment changes next week. Annual pen tests produce a point-in-time report that goes stale the day it's published. SCYTHE runs continuously, so your coverage data reflects your environment as it actually exists today, not as it existed six months ago when the engagement ran.
How is SCYTHE different from the built-in validation in CrowdStrike or Microsoft Defender?
Native EDR validation tools test within their own control plane. SCYTHE tests the full response chain — does the EDR detection generate a usable SIEM alert? Does that alert trigger the right SOC workflow? Does a ticket get created? Those questions require a platform that sits above and across the stack, not inside a single tool.
Do we need an internal red team to get value from SCYTHE?
No. SCYTHE is used by organizations at every maturity level, from teams with no red team running automated EDR and SIEM validation, to enterprise red teams running complex multi-stage campaigns. The platform scales to what your team needs. SCYTHE also offers Managed AEV for organizations that want continuous validation without building an internal capability.
How does SCYTHE integrate with existing security tools?
SCYTHE integrates bi-directionally with SIEM, SOAR, EDR, ticketing systems, and security controls. Teams can automate validation workflows, measure detection quality, and optionally suppress SOC alerts during controlled testing to reduce analyst fatigue.
Can SCYTHE support continuous detection engineering?
Yes. SCYTHE enables teams to test SIEM rules, validate new CTI-driven detections, and regression-test detection logic when infrastructure or tooling changes.
How long does implementation take?
Most organizations run their first campaign within hours of deployment. Initial integration with EDR and SIEM platforms is typically completed in one to two weeks. Value compounds as campaigns are scheduled and detection coverage tracking matures over the following weeks and months.
How does SCYTHE handle compliance and audit requirements?
SCYTHE produces defensible, repeatable evidence of control effectiveness, dated test results, technique-level outcomes, and ATT&CK coverage data. This supports frameworks including NERC CIP, IEC 62443, NIST CSF, and TSA security directives, and provides the evidence base auditors and regulators look for beyond documentation alone.
Is SCYTHE safe to run in production environments?
Yes. SCYTHE is designed for production-safe emulation. Every test is controlled, configurable, and scoped to your operational risk tolerance. Destructive capabilities require explicit authorization. All actions are logged and auditable. SCYTHE is widely deployed in live IT, cloud, and OT environments including regulated industries where operational availability is non-negotiable.
How does pricing work?
GET EXPERT ADVISE
Cybersecurity strategy with SCYTHE.
SCYTHE turns adversary simulation into a continuous program, not a point-in-time exercise. High-fidelity threat emulation and automated control validation give security teams the evidence they need: what their controls catch, what they miss, and where gaps are widening. Flexible deployment across IT, cloud, OT, and AI attack surfaces means validation keeps pace with the environment, not the other way around.
Request Demo
RESOURCE LIBRARY
Most Downloaded Resources
Contact Us
Welcome to SCYTHE, your partner in understanding and defending against cyber attacks. We appreciate your interest in enhancing your cybersecurity defenses.
Please fill the form to reach out to our dedicated team.