Resources
Threat Intel & Resources
"Built for the people doing the work, not for marketing."
Weekly threat analysis from our red team. A campaign library mapped to MITRE ATT&CK. Live and on-demand video. Practitioner guides for security leaders building mature offensive programs. Everything here is free.
Overview
What you'll find
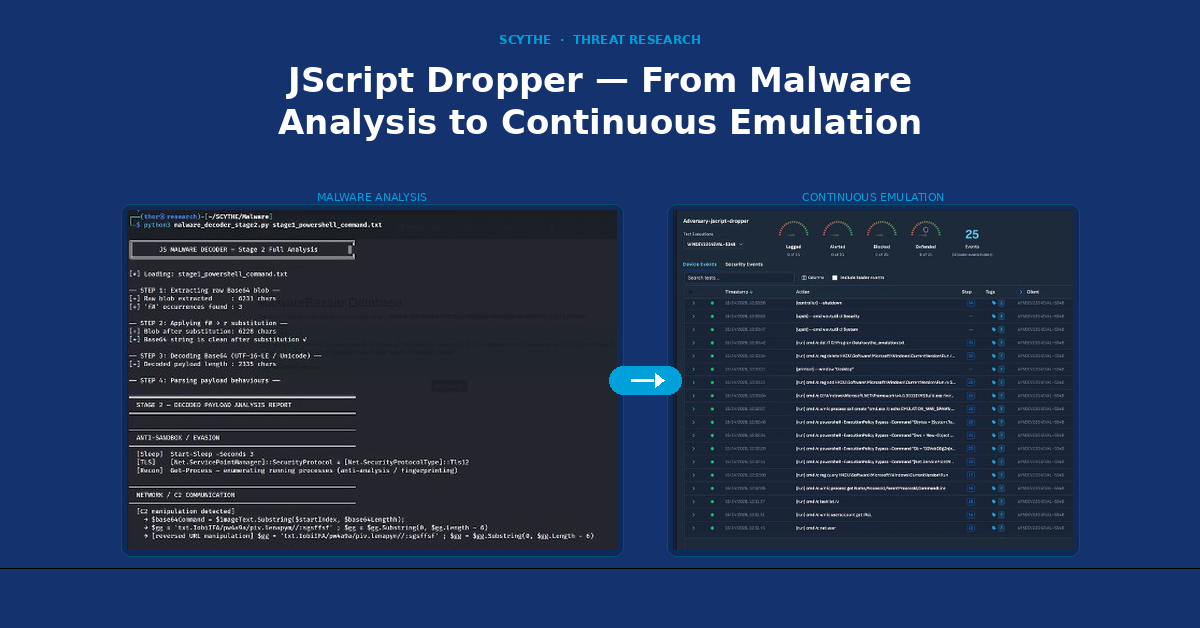
Threat Thursday
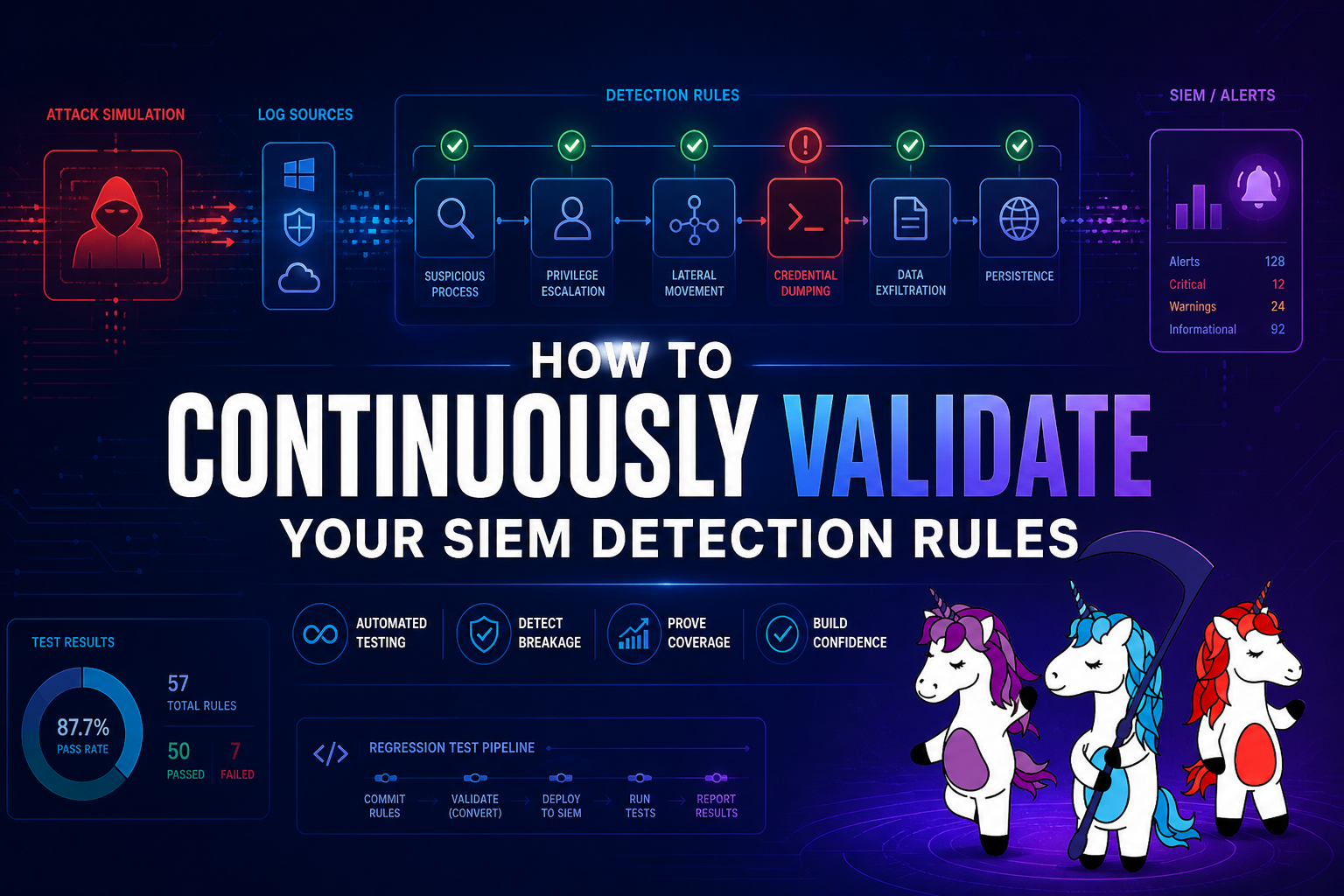
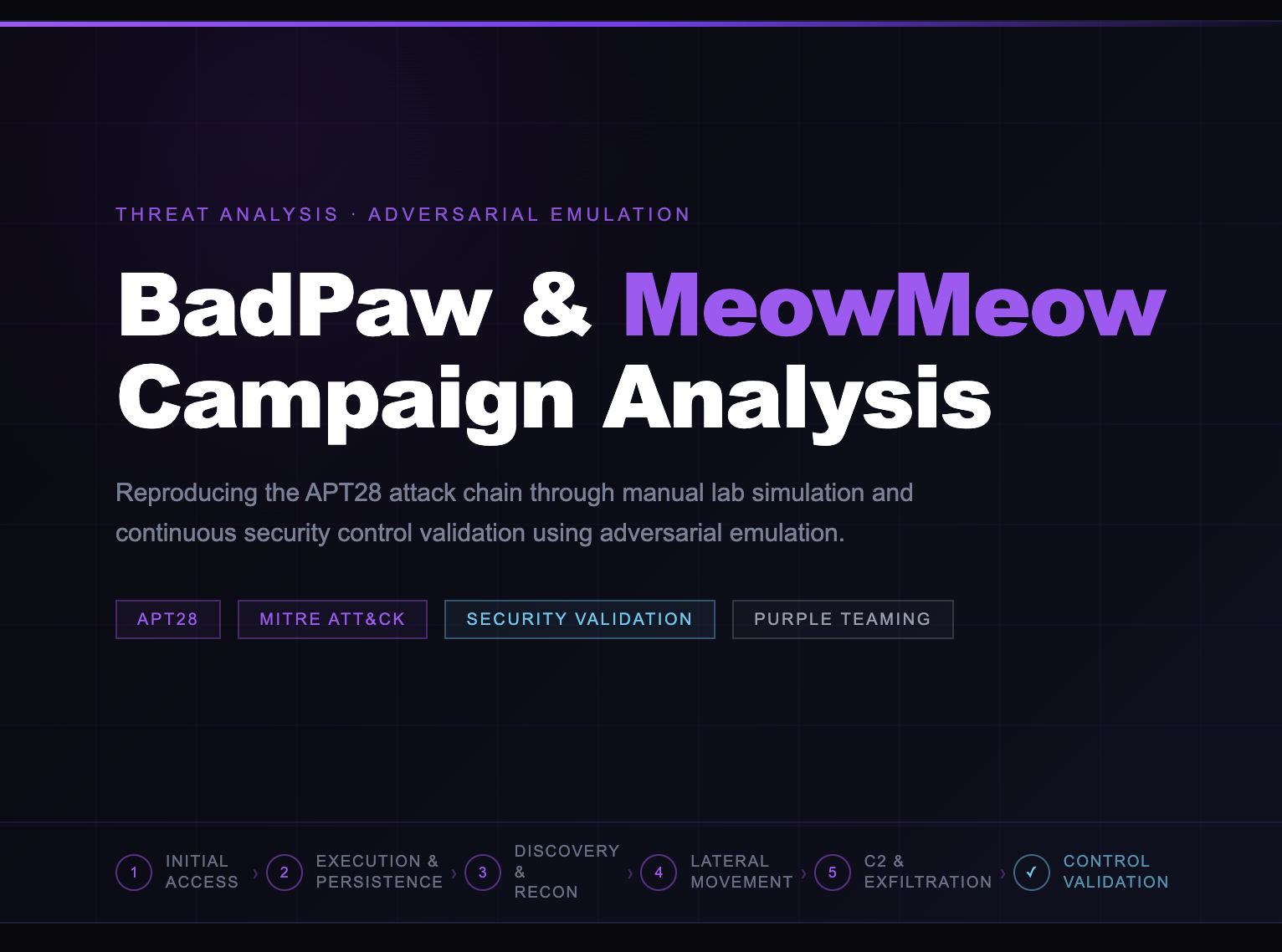
Weekly breakdowns of real adversary techniques, how they work, how to emulate them, and how to validate whether your defenses catch them.
SCYTHE Labs & Blogs Library
In-depth threat actor profiles, adversarial emulation analyses, and technical research. Named actors. Real TTPs. MITRE ATT&CK mapped.
Watch
Live and recorded sessions from Threat Thursday Live and Unicorn Dispatch Live, practitioner discussions, threat walkthroughs, and platform demos on YouTube.
Downloads
Frameworks, guides, and research reports for practitioners and security leaders. Free, no form-fills for most resources.
Watch
Live & On-Demand
Practitioner-led sessions from the SCYTHE team — threat walkthroughs, adversary emulation demos, and red/blue team discussions. Subscribe to catch new episodes live.
Weekly
Threat Thursday Live
Trey & Tyler | SCYTHE Labs
Join SCYTHE's red team every Thursday for live adversary technique breakdowns, MITRE ATT&CK walkthroughs, and emulation demos.
Watch PlaylistSeries
Unicorn Dispatch Live
Hosted by Bryson Bort, SCYTHE Founder & CEO
Longer-form conversations with security practitioners, threat researchers, and platform experts on adversarial emulation strategy and defensive operations.
Watch PlaylistThreat News
Labs, Threat Thursday & More





SCYTHE Blogs
Articles, News, and Opinions

.png)


SCYTHE DOWNLOADABLES
eBooks, eBuides, and more.
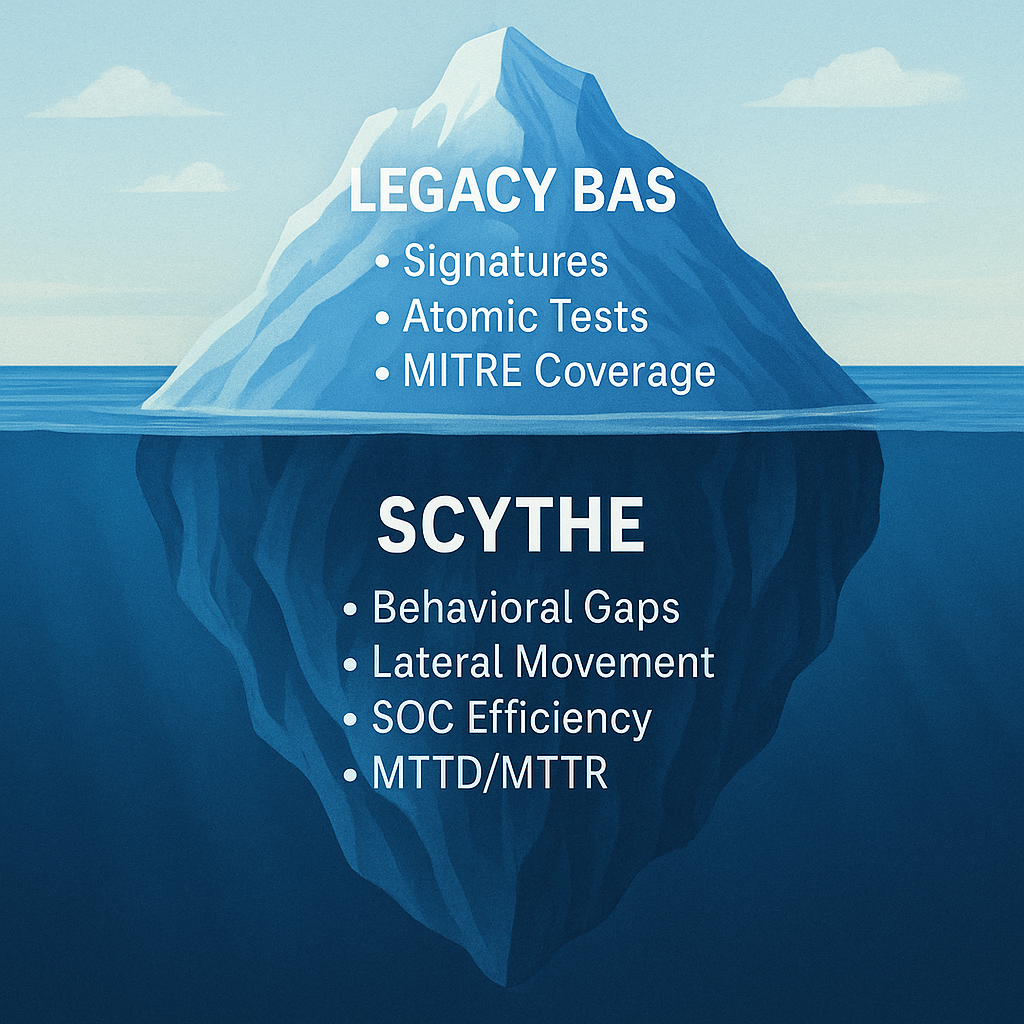
A Guide to Adversarial Emulation & Validation (AEV)
Your organization should undergo regular security posture assessments which serve as your annual cybersecurity physical, providing insights into your organization.
Cyber Fitness Guide
Your organization should undergo regular security posture assessments which serve as your annual cybersecurity physical, providing insights into your organization.
Offensive Cybersecurity Maturity
For security leaders looking to navigate this challenging landscape, developing a comprehensive, forward-looking strategy is essential.
Cybersecurity Fitness Guide
This annual cyber fitness guide is designed to help you baseline your cyber risk, validate cyber hygiene, assess your cyber readiness.
Red Team Operations Roadmap
This eBook serves as a comprehensive roadmap for organizations at any stage of their Red Team maturity.
Adversarial Behavior Detection
The threat landscape continues to evolve, driving continuous transformation across all industries, IT and OT/ICS professions, and regulations.
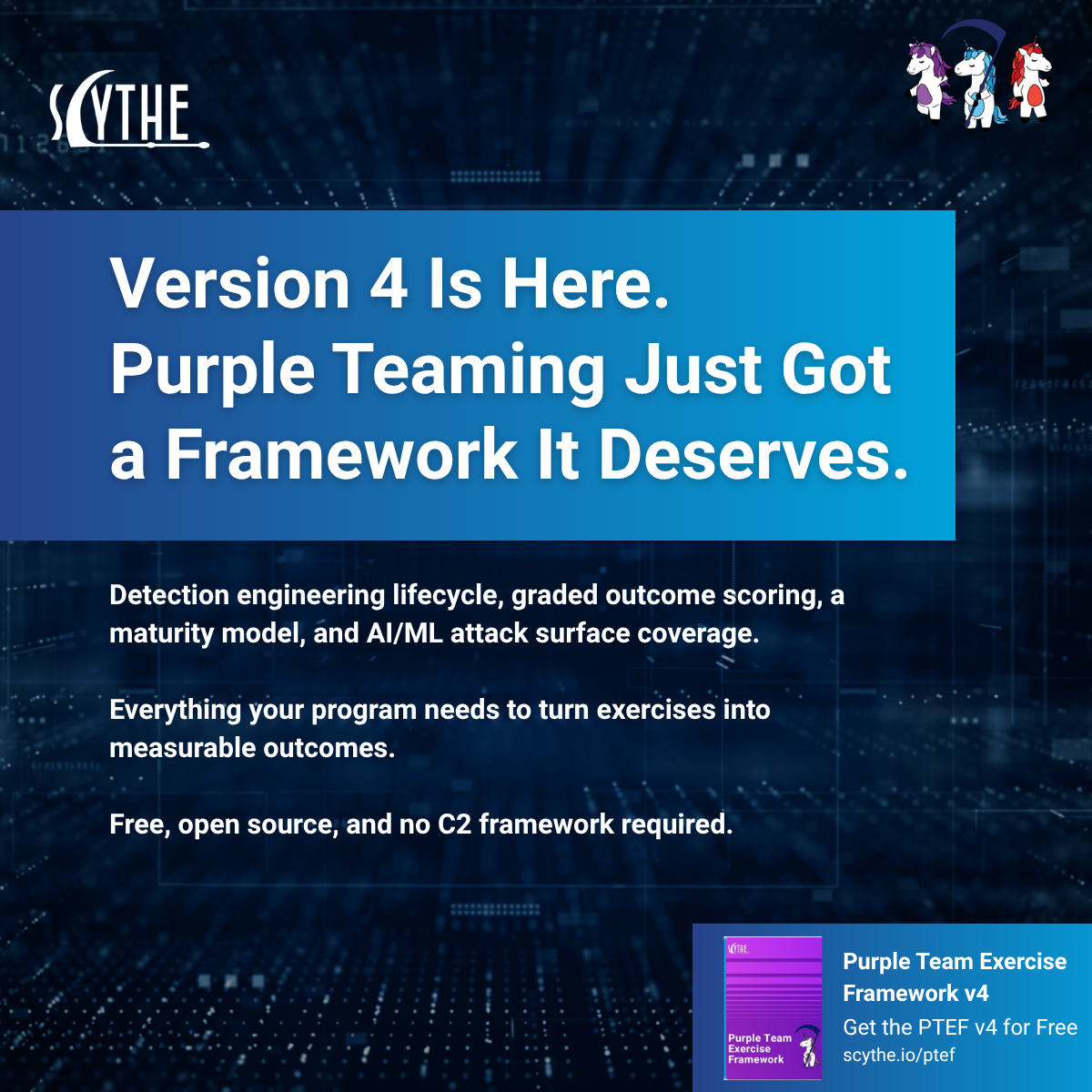
CISOs Guide to Purple Teaming
The SCYTHE Purple Team Exercise Framework (PTEF) provides a structured path for organizations to build...
Contact Us
Contact Us
Welcome to SCYTHE, your partner in understanding and defending against cyber attacks. We appreciate your interest in enhancing your cybersecurity defenses.
Please fill the form to reach out to our dedicated team.
.png?width=1414&height=2000&name=Leveraging%20SCYTHE%20for%20Continuous%20Threat%20Exposure%20Management%20(CTEM).png)


.jpg?width=375&height=480&name=6113d4154362581e847c985d_ptef%20v2-p-500-2%20(1).jpg)