Opinion Purple Teaming Controls Validation Compliance & Frameworks
You're spending six figures on an annual pentest that tells you what's broken but not whether your team can fix it under pressure. Purple Team Exercises combined with tabletop exercises deliver everything a pentest does — and everything it doesn't.
SCYTHE · April 2026 · 10 min read
Let's be direct: the annual penetration test, as most organizations run it, is a compliance ritual that produces a PDF, checks a box, and changes almost nothing.
An external team spends two weeks finding vulnerabilities your scanner already flagged. They rate them Critical, High, Medium, Low. They hand you a report. Your team triages the findings, patches what they can, accepts the risk on the rest, and files the report in a compliance folder until the next audit asks for it. Rinse, repeat, year after year.
Meanwhile, your SOC has never practiced responding to a real intrusion. Your IR playbook has never been tested under pressure. Your blue team has never seen what an adversary's post-access behavior actually looks like in their SIEM. And when the real attack comes — not the pentest, the real one — the first time your team encounters a living-off-the-land attack chain is the day they have to contain it.
There's a better way. And it still satisfies ISO 27001, PCI DSS, SOC 2, DORA, TIBER-EU, and every other framework that requires "penetration testing" — while delivering dramatically more value.
The Argument
Replace your annual pentest with Purple Team Exercises combined with Tabletop Exercises — what we call a Hybrid TTX. You get everything the pentest delivered (vulnerability findings, control validation, compliance evidence) plus everything it never could: measured detection and response times, tested IR playbooks, trained defenders, and validated security operations across people, process, and technology. Same budget. Ten times the outcome.
The Pentest Problem Nobody Talks About
Pentesting was invented for a world where the primary question was "can someone get in?" That was a reasonable question in 2005. In 2026, the answer is always yes. The question that matters now is: when they get in, does your team detect it, contain it, and respond before business impact?
Here's what your annual pentest doesn't tell you:
Snapshot, not film
A pentest captures your posture on one day. Threats evolve weekly. By the time you remediate the findings, the attack surface has shifted. You're patching yesterday's picture while today's adversaries walk through a different door.
Technology only
Pentests evaluate whether a vulnerability is exploitable. They don't test whether your SOC analyst sees the alert, whether the runbook escalates it correctly, or whether your IR team contains the spread. People and process are 70% of the problem. Pentests ignore them entirely.
Zero knowledge transfer
External pentesters work in a silo. They find vulnerabilities, write a report, and leave. Your blue team learns nothing about how the attacks were executed, what the telemetry looked like, or how to detect similar techniques in the future. The engagement ends and the knowledge walks out the door.
Severity in a vacuum
Pentest findings are rated by technical severity — not by whether your layered defenses mitigate the risk. A "Critical" vulnerability that your EDR blocks at execution is not the same risk as a "Medium" finding that bypasses every control. Without context, the prioritization is wrong.
The Hybrid TTX: Purple Team Exercise Meets Tabletop Exercise
A Hybrid TTX combines two exercises that most organizations run separately — and poorly — into one engagement that delivers more value than either alone.
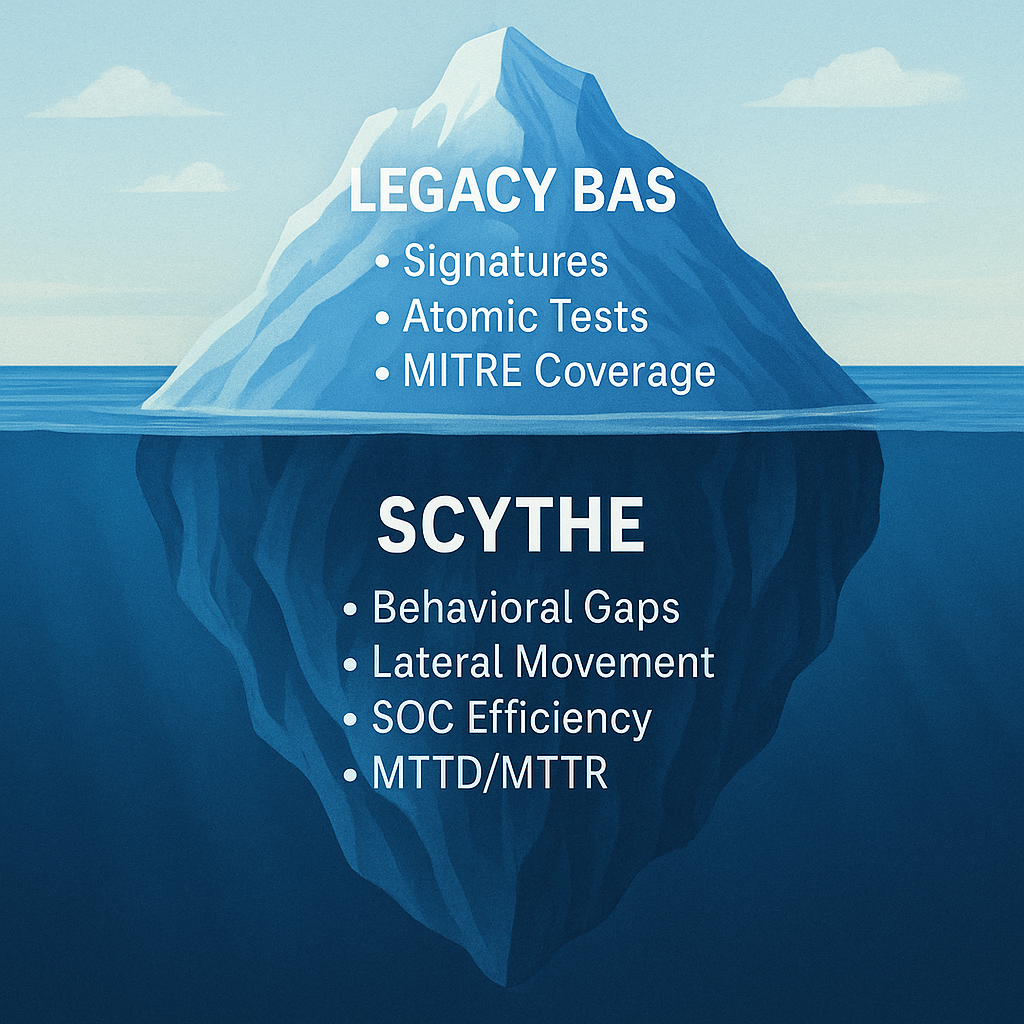
The Purple Team Exercise (PTE) is the technical half. Red and blue teams work together — not adversarially — to execute real adversary TTPs against your production environment. The red team runs an emulation campaign mapped to MITRE ATT&CK. The blue team watches their tools in real time. Both teams see what gets detected, what gets missed, and iterate on detections together. At the end, you have measured time-to-detect, validated controls, and tuned detection rules — not just a list of vulnerabilities.
The Tabletop Exercise (TTX) is the strategic half. Leadership, IR teams, legal, communications, and business stakeholders walk through the incident response scenario — but instead of a hypothetical scenario written by a consultant, they're reacting to the real data generated by the PTE. Real alerts. Real timelines. Real gaps. The discussion isn't abstract; it's grounded in what just happened in their own environment.
Combined, the Hybrid TTX tests everything: technical controls, analyst performance, process effectiveness, escalation paths, communication protocols, and executive decision-making. In a single engagement.
| |
Annual Pentest |
PTE Alone |
Hybrid TTX |
| Finds vulnerabilities |
✓ |
✓ |
✓ |
| Tests controls against real TTPs |
— |
✓ |
✓ |
| Measures detection time |
— |
✓ |
✓ |
| Trains blue team |
— |
✓ |
✓ |
| Tests IR playbooks under pressure |
— |
— |
✓ |
| Exercises executive decision-making |
— |
— |
✓ |
| Tests cross-team communication |
— |
— |
✓ |
| Identifies policy & process gaps |
— |
Partial |
✓ |
| Satisfies compliance requirements |
✓ |
✓ |
✓ |
| Knowledge stays in-house |
— |
✓ |
✓ |
How to Make the Case to Leadership
The most common objection is: "Our compliance framework requires a penetration test. We can't replace it." Here's the reality: most frameworks require threat-led testing or security assessment — and a Purple Team Exercise satisfies those requirements with a stronger deliverable.
Here's how the Hybrid TTX maps to the frameworks that matter:
ISO 27001 (Annex A.12.6, A.18.2)
Requires "technical compliance review" and vulnerability management. A PTE produces vulnerability findings (same as a pentest) plus validated detection coverage and measured response times. Auditors accept PTE reports because they exceed the evidentiary standard — you're showing not just what's broken but whether your controls catch adversary behavior.
PCI DSS 4.0 (Requirement 11.4)
Requires penetration testing that includes network-layer and application-layer tests. PCI DSS 4.0 explicitly encourages threat-informed approaches. A PTE using adversary emulation against your cardholder data environment delivers the required scope — with the added benefit of testing whether your monitoring detects the simulated breach, which PCI increasingly expects.
SOC 2 Type II (CC7.1, CC7.2)
Requires monitoring, detection, and response to security incidents. A Hybrid TTX produces evidence of tested detection and response capabilities — exactly what SOC 2 auditors look for. The PTE demonstrates control effectiveness; the TTX demonstrates incident management process maturity.
DORA & TIBER-EU
These frameworks were explicitly designed around threat-led penetration testing — they require adversary emulation by definition. TIBER tests are essentially PTEs with regulatory oversight. If your organization operates under DORA or TIBER, you're already required to do what we're describing. The Hybrid TTX simply adds the tabletop layer that makes the exercise valuable beyond the technical findings.
The AI Factor: Why Annual Testing Is No Longer Enough
Here's where the argument gets urgent. In a world where adversaries are using AI to generate polymorphic payloads, automate initial access, and adapt attack chains based on the defenses they encounter — testing once a year is like checking your smoke detector once a decade.
AI-generated threats evolve weekly. New CVEs are weaponized within hours of disclosure. Ransomware groups are automating lateral movement. The attack surface changes every time someone deploys a new cloud workload, opens a new SaaS integration, or onboards a new vendor.
The Hybrid TTX model supports continuous execution — run a PTE quarterly, monthly, or even on-demand when a new threat advisory drops. Each run produces fresh data, validates current defenses against current threats, and feeds the tabletop discussion with real intelligence rather than hypothetical scenarios from a consultant's slide deck. Platforms with AI-assisted campaign building make this practical even for lean teams: describe the threat, generate the campaign, execute, and measure — in hours, not weeks.
How to Run Your First Hybrid TTX
You don't need to overhaul your security program overnight. Start by replacing your next scheduled annual pentest with a Hybrid TTX:
Step 1 — Select the Threat
Use threat intelligence to identify 1–2 named threat actors most likely to target your industry. Build or import an adversary emulation campaign mapped to their known TTPs. With SCYTHE, this can be done from the pre-built threat library or generated using AI-assisted campaign building in minutes.
Step 2 — Execute the PTE
Run the campaign against your production environment with both red and blue teams in the room. Red executes the attack chain. Blue monitors their tools. Both teams log time-to-detect, time-to-respond, and gaps in coverage. Pause, discuss, tune, and replay techniques that were missed. This is where the real learning happens.
Step 3 — Run the Tabletop
Immediately after the PTE, convene the broader team — IR, leadership, legal, comms — for a tabletop exercise using the real data from the PTE. Walk through the timeline: when was initial access achieved, when was it detected, what was the escalation path, where did communication break down, what decisions were made and how fast. This isn't a hypothetical. It just happened in your environment.
Step 4 — Document and Repeat
Package the results: vulnerability findings (pentest equivalent), detection coverage (controls validation), response metrics (people and process), and leadership observations (governance). This single deliverable satisfies your compliance requirement and gives you a baseline to measure against next quarter. Schedule the next one.
Stop Paying for a PDF. Start Building Resilience.
Your annual pentest tells you what's broken. A Hybrid TTX tells you whether your organization can survive an attack. One produces a report. The other produces a team that knows how to fight.
The compliance box gets checked either way. The difference is what your organization actually learns in the process.


.png)
.png)