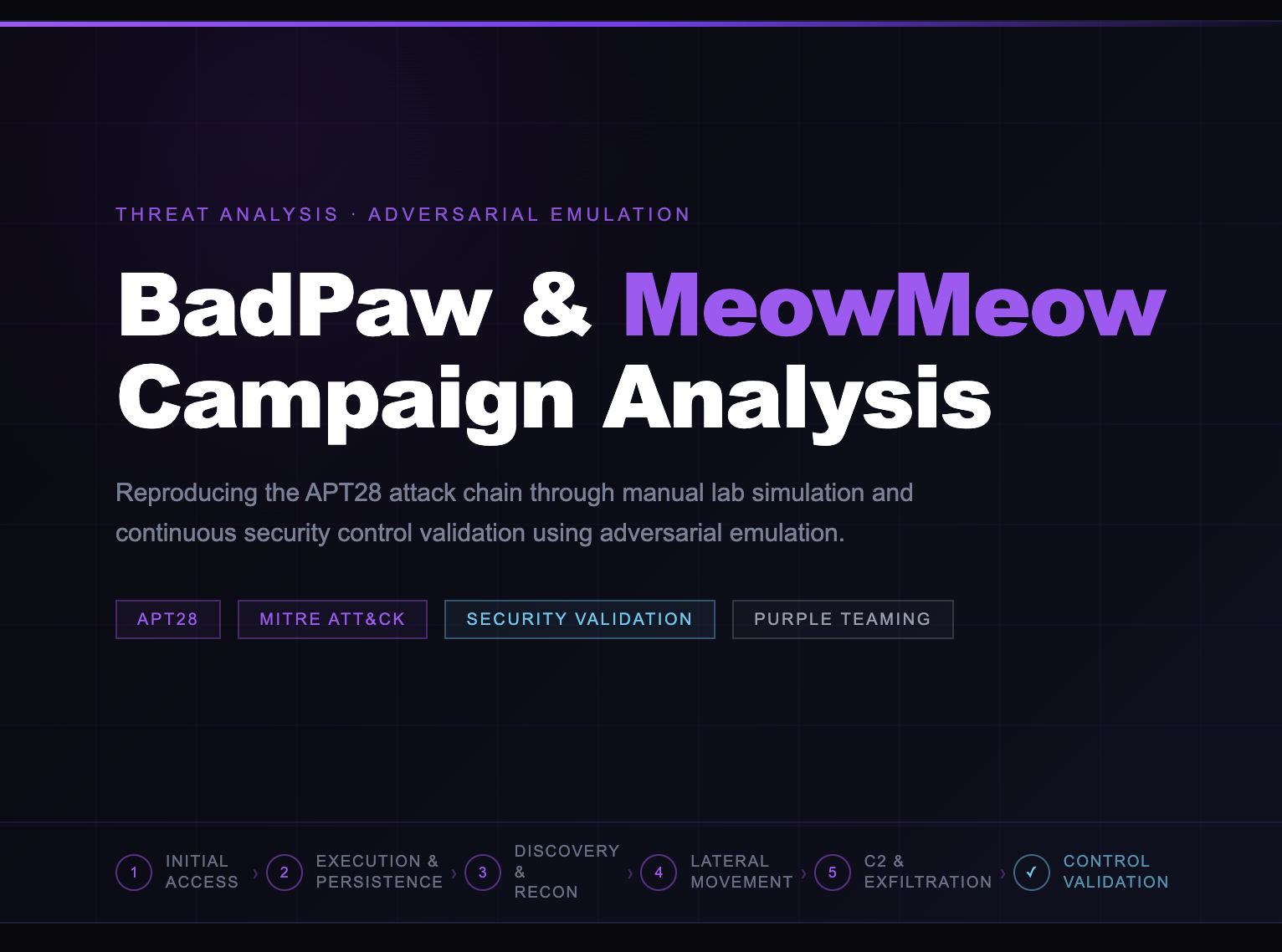
A technical analysis of the APT28 BadPaw/MeowMeow campaign, showing how manual lab simulation and SCYTHE adversarial emulation can be used to reproduce the attack chain and continuously validate whether security controls detect and stop it.
APT28 — BadPaw / MeowMeow: From Manual Lab to Continuous Emulation
A technical analysis of the APT28 BadPaw/MeowMeow campaign, showing how manual lab simulation and SCYTHE adversarial emulation can be used to ...
|
APT28 Threat Actor |
BadPaw Loader |
MeowMeow RAT |
9 Attack Phases |
42 SCYTHE Events |

Figure 1 — ClearSky Cyber Security: APT28 BadPaw/MeowMeow campaign chain
1. Executive Summary
APT28, also known as Fancy Bear, Sofacy, and STRONTIUM, is a Russian military intelligence (GRU) unit responsible for some of the most sophisticated cyber espionage campaigns of the past decade. In early March 2026, threat intelligence firm ClearSky Cyber Security reported a new active campaign targeting Ukrainian government and energy organizations, leveraging two custom tools: BadPaw, a PNG steganography-based loader, and MeowMeow, a full-featured Remote Access Trojan.
This article documents two complementary approaches to understanding and validating defenses against this threat: a manual lab simulation conducted in an isolated environment using open-source tools, and an adversarial emulation campaign built and executed on the SCYTHE Adversarial Emulation & Validation platform. Together, they illustrate the gap between understanding an attack and continuously proving your controls work against it.
|
KEY INSIGHT Two Approaches, One Goal A manual lab tells you HOW the attack works. SCYTHE tells you whether your security controls would DETECT and STOP it, and gives you that answer every time you run it, against every environment change. |
2. Threat Intelligence — BadPaw & MeowMeow
The BadPaw/MeowMeow campaign represents a mature, multi-stage operation consistent with APT28's documented operational tradecraft. The attack chain begins with a spearphishing email delivering a ZIP archive containing an HTA file, which executes a VBScript dropper that ultimately deploys the BadPaw loader.
2.1 BadPaw — Steganographic Loader
BadPaw is responsible for initial execution and anti-analysis. It reads an encoded payload concealed within a PNG image file using steganography. When executed without a specific command-line parameter (-v flag), BadPaw enters a GUI mode that functions as a decoy application a deliberate sandbox evasion mechanism. Only when invoked with the correct parameter does it proceed to extract and execute the MeowMeow payload.
2.2 MeowMeow — Full-Featured RAT
MeowMeow provides the attacker with persistent remote access and a broad capability set mapped across multiple MITRE ATT&CK tactics:
- PowerShell execution (T1059.001)
- File read, write, and deletion (T1005)
- Scheduled task creation for persistence (T1053.005)
- Credential harvesting via registry hive dump (T1003.002)
- Keylogging and screen capture (T1056.001, T1113)
- Exfiltration over C2 channel and web services (T1041, T1567)
|
MITRE Technique |
Tactic |
Tool |
Description |
|
T1059.001 |
Execution |
MeowMeow |
PowerShell command execution |
|
T1003.002 |
Credential Access |
MeowMeow |
SAM registry hive dump |
|
T1053.005 |
Persistence |
MeowMeow |
Scheduled task — EventCacheManager |
|
T1547.001 |
Persistence |
MeowMeow |
Startup folder + logon script |
|
T1056.001 |
Collection |
MeowMeow |
Keylogging |
|
T1113 |
Collection |
MeowMeow |
Screen capture |
|
T1041 |
Exfiltration |
MeowMeow |
Exfil over C2 channel |
|
T1567.002 |
Exfiltration |
MeowMeow |
Exfil to web service (file.io) |
|
T1070.001 |
Defense Evasion |
MeowMeow |
Event log clearing |
|
T1497.003 |
Defense Evasion |
BadPaw |
Time-based sandbox evasion |
3. Manual Lab Simulation
The manual lab simulation was conducted in an isolated virtual environment to reproduce the APT28 attack chain from initial access through exfiltration and cleanup. The lab consisted of a Kali Linux attack host (172.16.146.241) and a Windows 10 target (172.16.146.240), connected on an isolated network segment. The target was also connected to a secondary subnet (192.168.1.111) to simulate a dual-homed endpoint common in enterprise environments.
|
PHASE 1 |
PHASE 1 [ T1105, T1071.001 ] |
Initial Access & C2 Establishment
After network reconnaissance confirmed port 445 open with SMB signing disabled, a Metasploit payload (gdrive.exe — 7,680 bytes) was generated using msfvenom and delivered to the target via a Python HTTP server. The victim executed the payload via PowerShell Start-Process, establishing a Meterpreter reverse HTTPS session on port 4444.

Figure 2 — msfvenom generating gdrive.exe payload (7,680 bytes, SHA256: 1ce2064e...)

Figure 3 — Meterpreter session 1 opened: DESKTOP-1A6OUL8\Administrator via reverse HTTPS
|
PHASE 2 |
PHASE 2 [ T1082, T1016, T1049 ] |
Post-Compromise Discovery
With an active Meterpreter session, the attacker performed systematic host and network reconnaissance. The ipconfig output revealed that the target was dual-homed, connected to both the lab network (172.16.146.240) and a secondary subnet (192.168.1.111), identifying a potential lateral movement path.

Figure 4 — ipconfig /all reveals dual-homed target: 172.16.146.240 + 192.168.1.111
|
PHASE 3 |
PHASE 3 [ T1003.002 ] |
Credential Access — SAM Registry Hive Dump
The three Windows registry hives required for offline credential extraction (SAM, SECURITY, SYSTEM) were dumped via reg save commands executed from an elevated shell. The hive files were downloaded to the Kali host and processed using impacket-secretsdump, successfully extracting the local Administrator NTLM hash.

Figure 5 — reg save dumping SAM, SECURITY, and SYSTEM hives to %PROGRAMDATA%

Figure 6 — impacket-secretsdump extracting NTLM hash: Administrator:b73fdfe10e87b4ca...
|
CRITICAL FINDING NTLM Hash Extracted Administrator NTLM hash b73fdfe10e87b4ca5c0d957f81de6863 was extracted in under 90 seconds from initial shell access. This hash enables Pass-the-Hash lateral movement to any system where the same administrator password is reused a common finding in enterprise environments. |
|
PHASE 4 |
PHASE 4 [ T1547.001, T1053.005 ] |
Persistence — Three Independent Mechanisms
Three persistence mechanisms were installed simultaneously, mirroring APT28's documented layered persistence strategy. This ensures that removal of any single mechanism does not eliminate access. The scheduled task was deliberately named EventCacheManager under \Microsoft\Windows\SoftwareProtectionPlatform, a masquerade (T1036) of a legitimate Windows subsystem path.

Figure 7 — All three persistence mechanisms confirmed: startup folder, registry logon script, scheduled task
|
PHASE 5 |
PHASE 5 [ T1041, T1567 ] |
Exfiltration — Dual Channel
Data exfiltration occurred over two simultaneous channels. The credential archive (out.zip, 2.8MB) was transmitted over the established Meterpreter C2 channel. The document collection (exfil.zip, 25MB) was exfiltrated using curl via an HTTP POST to file.io, blending with legitimate web traffic. Both channels succeeded without triggering any security controls.

Figure 8 — Windows: curl exfiltrating exfil.zip via HTTPS POST to file.io

Figure 9 — Kali: Meterpreter receiving out.zip (2.8MB) via C2 channel — transfer complete
4. SCYTHE Adversarial Emulation
After completing the manual lab, the same attack chain was codified as a SCYTHE threat profile and executed against the same Windows endpoint using SCYTHE's Adversarial Emulation & Validation platform. This transforms the one-time lab exercise into a repeatable, measurable, and continuously executable validation campaign.
4.1 Threat Profile Setup
The threat was imported into SCYTHE's Test Library as Adversary-Apt28-2026-03-BadPaw. The profile is tagged with relevant sectors (Energy, Government, APT28) and carries the full MITRE ATT&CK TTP mapping automatically surfaced by the platform from the script's rtags.

Figure 10 — SCYTHE Threat Details: tags, description, and MITRE TTPs auto-populated from script rtags
4.2 Attack Sequence — Full Script
The attack sequence is built as a numbered step graph in SCYTHE's visual editor. Each step carries its module, request parameters, and ATT&CK rtags. The sequence begins with capability loading (steps 0–7) followed by seven behavior phases, each marked with an assign step that groups related techniques under a named behavior label.

Figure 11 — Attack Sequence: initialization (HTTPS C2) + capability loaders (steps 0–8, Behavior = Discovery)

Figure 12 — Discovery (T1046, T1057, T1082, T1016, T1049, T1033) + Credential Access (T1003.002 × 3 hives + T1560.001)

Figure 13 — Collection: keylogger start, staging directory, file create, compress, printscr, keylogger stop

Figure 14 — Persistence (T1105, T1547.001 × 2, delay T1497.003) + Exfil (T1041, T1567.002) + Payload Execution (T1053.005)
4.3 Campaign Execution
The campaign was deployed to DESKTOP-1A6OUL8 under test APT28_BADPAW. The SCYTHE agent ran as PID 9572, generating 42 device events. All 54 steps executed successfully, progressing through all seven behavior phases in sequence.

Figure 15 — Campaign APT28_BADPAW: ACTIVE on DESKTOP-1A6OUL8, PID 9572, 42 events — 03/11/2026
4.4 Remote Access — Live Shell via SCYTHE
One of SCYTHE's most operationally powerful features is the Remote Access capability, which provides security teams with a live interactive shell to the compromised endpoint directly from the platform. This allows red team operators to perform ad-hoc commands alongside the automated campaign, here demonstrating the SCYTHE agent running as NT AUTHORITY\SYSTEM on the target host.

Figure 16 — SCYTHE Remote Access option available directly from the campaign execution row

Figure 17 — Live SCYTHE remote shell: run whoami → autoridade nt\sistema (NT AUTHORITY\SYSTEM) | run hostname → DESKTOP-1A6OUL8
4.5 Device Events Timeline
The Device Events view provides a complete timestamped log of every step executed by the campaign, with step numbers, ATT&CK tags, and execution status. This timeline is the primary artifact for blue team analysis — mapping each event to a detection opportunity and confirming execution sequence integrity.

Figure 18 — Device Events timeline: steps 39–54 (Defense Evasion + cleanup) — all executed successfully
4.6 Threat Indicators — Automated Behavioral Analysis
SCYTHE automatically analyzes each executed step and generates Threat Indicators based on behavioral patterns. One particularly important indicator that surfaced during this campaign, demonstrating this pertained to event log clearing:
.png?width=818&height=483&name=image%20(15).png)
Figure 19 — Step 42 (wevtutil cl Application): Threat Indicator "Superuser/Administrator Access" — Confidence 10/10 (High)
The wevtutil event log clearing step triggered a Superuser/Administrator Access indicator at maximum confidence (10/10 High) correctly identifying that this action requires and demonstrates elevated privileges, and is a high-fidelity indicator of a post-compromise cleanup operation.
5. MITRE ATT&CK Coverage & Detection Gaps
At the conclusion of the campaign, SCYTHE generates a full MITRE ATT&CK coverage report mapping every executed technique to its detection status — Blocked, Logged, Alerted, or Gap. This report is the primary deliverable for security teams to prioritize control improvements.
5.1 ATT&CK Navigator Heatmap

Figure 20 — SCYTHE MITRE ATT&CK Navigator layer: techniques highlighted across 7 tactics from the APT28_BADPAW campaign
The Navigator heatmap provides an immediate visual representation of which portions of the ATT&CK matrix were exercised by the campaign. Highlighted techniques span Execution, Persistence, Defense Evasion, Credential Access, Discovery, Collection, Command and Control, and Exfiltration, covering the full operational scope of the BadPaw/MeowMeow campaign.
5.2 Coverage Report — Blocked vs. Gaps

Figure 21 — SCYTHE MITRE ATT&CK Coverage Report: Blocked (green) vs. Gap (red) per technique
The Coverage Report surfaces specific detection gaps that require remediation. In this campaign execution, the following findings were identified:
|
Technique |
Name |
Status |
Finding |
|
T1059 / T1059.001 |
Command and Scripting / PowerShell |
BLOCKED |
PowerShell execution policy or EDR rule triggered — control is working |
|
T1033 |
System Owner/User Discovery |
BLOCKED |
whoami execution detected and blocked by EDR |
|
T1056 |
Input Capture (Keylogging) |
GAP |
Keylogger activity not detected — no EDR coverage for T1056 |
|
T1007 |
System Service Discovery |
GAP |
portscan.ps1 execution not alerted — rule missing or disabled |
|
T1057 |
Process Discovery |
GAP |
tasklist pipe to findstr not generating detection event |
|
DETECTION GAP Keylogging — T1056 Not Detected The keylogger running for the entire Collection phase (steps 21–28) generated zero detection events. This is a critical gap: in a real APT28 engagement, keylogged credentials would be exfiltrated silently. Recommended mitigation: implement EDR behavioral rule for processes calling SetWindowsHookEx or GetAsyncKeyState APIs. |
6. Manual Lab vs. SCYTHE — Approach Comparison
Both approaches are complementary and serve distinct purposes in a mature security validation program. The manual lab provides a deep technical understanding of the attack mechanics. SCYTHE provides continuous, measurable validation of security controls at scale.
|
Dimension |
Manual Lab (Metasploit/Kali) |
SCYTHE Emulation |
|
Purpose |
Understand HOW the attack works |
Prove WHETHER controls detect it |
|
Repeatability |
Manual — effort each execution |
Automated — run on schedule or trigger |
|
Evidence |
Screenshots + command output |
Timestamped events + MITRE coverage report |
|
MITRE Mapping |
Manual tagging post-exercise |
Automatic — rtags on every step |
|
Detection Validation |
Requires separate SIEM/EDR review |
Built-in — Logged/Alerted/Blocked/Gap |
|
Threat Indicators |
Analyst judgment |
Automated behavioral analysis |
|
Time to Execute |
3–4 hours (full lab) |
~18 minutes (automated) |
|
Scalability |
One target at a time |
Multi-endpoint, continuous |
|
Reporting |
Manual write-up |
Auto-generated Coverage Report + Navigator layer |
7. Conclusion
The APT28 BadPaw/MeowMeow campaign demonstrates that a Tier-1 nation-state actor can move from initial access to credential theft, persistent access, and multi-channel exfiltration in under 20 minutes on an endpoint with no active detection controls. Every technique in this chain is documented, reproducible, and testable.
The manual lab exercise proves the attack is real and executable. The SCYTHE emulation proves something more operationally important: which specific controls are working and which are failing right now, in your environment, against this exact threat.
The detection gaps identified in this campaign particularly the complete absence of keylogging detection (T1056) and the undetected process discovery operations represent real-world risk that would otherwise remain invisible until a genuine APT28 intrusion revealed them. With SCYTHE, those gaps surface in a controlled environment, before the attacker does.
|
SCYTHE Adversarial Emulation & Validation SCYTHE enables security teams to continuously emulate real-world adversaries like APT28 and measure the effectiveness of their controls with empirical evidence — not assumptions. Whether for red team, blue team, or purple team operations, SCYTHE provides the clarity to stay ahead of evolving threats. Contact us at scythe.io to run this campaign against your environment. |
Latest Posts
Sign up to our newsletter
Sign up here to receive news and updates.