In response to escalating cybersecurity threats targeting the United State's critical pipeline infrastructure, including owners and operators of hazardous liquid and natural gas pipelines and liquefied natural gas (LNG) facilities, the U.S. Transportation Security Administration (TSA) stepped in with new regulations. The regulations aim to strengthen the cybersecurity framework by requiring pipeline operators to implement specific measures, such as improved cybersecurity practices, enhanced incident reporting, and more rigorous contingency and recovery plans.
These regulations enhance the security resilience of critical energy infrastructures by integrating advanced risk assessment methodologies and enforcing stringent cybersecurity protocols. This proactive approach mandates enhanced security practices and promotes an ongoing partnership among industry stakeholders, fostering a collaborative security environment. The evolution from the initial 2021 regulations to today's SD-02C framework demonstrates TSA's commitment to adapting its strategies to meet current and future security challenges.
The Timeline
May 2021: The TSA issued Pipeline-2021-01 that required asset owners to:
- Appoint a cybersecurity coordinator who will be a 24/7 POC.
- Report significant cybersecurity incidents to CISA as soon as practicable but no later than 12 hours after a cybersecurity incident is identified.
- Review their current activities against TSA's recommendations for pipeline cybersecurity to assess cyber risks, identify any gaps, develop remediation measures, and report the results to TSA and CISA.
July 2021: Two months later, TSA announced the second security directive, Pipeline-2021-02B with more prescriptive requirements, SD-02B mandated asset owners to:
- Implement specific mitigation measures to protect against ransomware attacks and other known threats to information technology and operational technology systems.
- Develop and implement a cybersecurity contingency and recovery plan.
- Conduct a cybersecurity architecture design review.
July 2022: The TSA issued an update SD-02C moving to a more flexible approach based on industry feedback (e.g., RSA Colonial Pipeline). Pipeline owners and operators must:
(e.g., RSA Colonial Pipeline). Pipeline owners and operators must:
- Establish and implement a TSA-approved Cybersecurity Implementation Plan;
- Develop and maintain a Cybersecurity Incident Response Plan to reduce the risk of operational disruption;
- Establish a Cybersecurity Assessment Program, and submit an annual plan that describes how the Owner/Operator will assess the effectiveness of cybersecurity measures. Specifically:
-
-
- Implement network segmentation policies and controls designed to minimize operational disruption to the Operational Technology system if the Information Technology system is compromised or vice versa;
- Implement access control measures, including for local and remote access, to secure and prevent unauthorized access to Critical Cyber Systems;
- Implement continuous monitoring and detection policies and procedures that are designed to prevent, detect, and respond to cybersecurity threats and anomalies affecting Critical Cyber Systems;
- Reduce the risk of exploitation of unpatched systems through the application of security patches and updates for operating systems, applications, drivers, and firmware on Critical Cyber Systems consistent with the Owner/Operator's risk-based methodology. It’s important to note, this directive includes the flexibility to document risk mitigations if patching is not an option, something we teach in our OT and Vulnerability Management classes.
July 2023: SD-02D:
- If you were not previously demarcated with Critical Cyber Systems, an asset owner must reevaluate upon a change in operations to determine whether they should notify the TSA to comply with the SD.
- No less than annually, test two CIRP (Cyber IR Plan) objectives: containment, segregation, security and integrity of back-up data, and isolation and include employees identified by position.
- CAP (Cyber Assessment Plan):
- At least 30% of policies, procedures, measures, and capabilities in the CIP are assessed each year, so 100% is covered every 3 years.
- Include an ADR (Architecture Design Review) every 2 years, including verifying and validating network traffic and system logs.
- Incorporate assessment capabilities such as the use of Red/Purple testing.
What We Know
Nation state actors, such as the People's Republic of China (PRC), and criminal cyber actors can significantly impact asset owner infrastructure from effects to production or business operations for strategic purposes or financial gain. USG and industry threat intelligence have reported since 2010 that these activities point toward preparation for future conflict with the United States. The PRC-affiliated actor Volt Typhoon utilizes techniques, such as living off the land (LOTL, which includes LOLBAS/LOLBIN techniques– see our repository for several years of emulation examples) to establish persistent and stealthy footholds (I have repeatedly referenced these publicly in my talks as "levers for future action") Volt Typhoon continues to target and pose a serious threat to U.S. critical infrastructure using Known Exploited Vulnerabilities (KEVs).
Recommendations
USG can only do so much, which is why the industry should consider the following recommendations to meet and reinforce what needs to be done:
- Know what you have (and how it works): asset management is the key foundation for operations and cybersecurity. It is not necessary to establish this in an automated fashion in control zones; there is a balance between real-time visibility and breaking segmentation. Sometimes, control over a segment is enough at a high level.
- Architect for defense: The intent behind the Purdue Model's control zones and conduits is to minimize impact through East-West segmentation while establishing monitoring overwatch at key North-South intersections. Proper architecture is the foundation for proper network operational visibility.
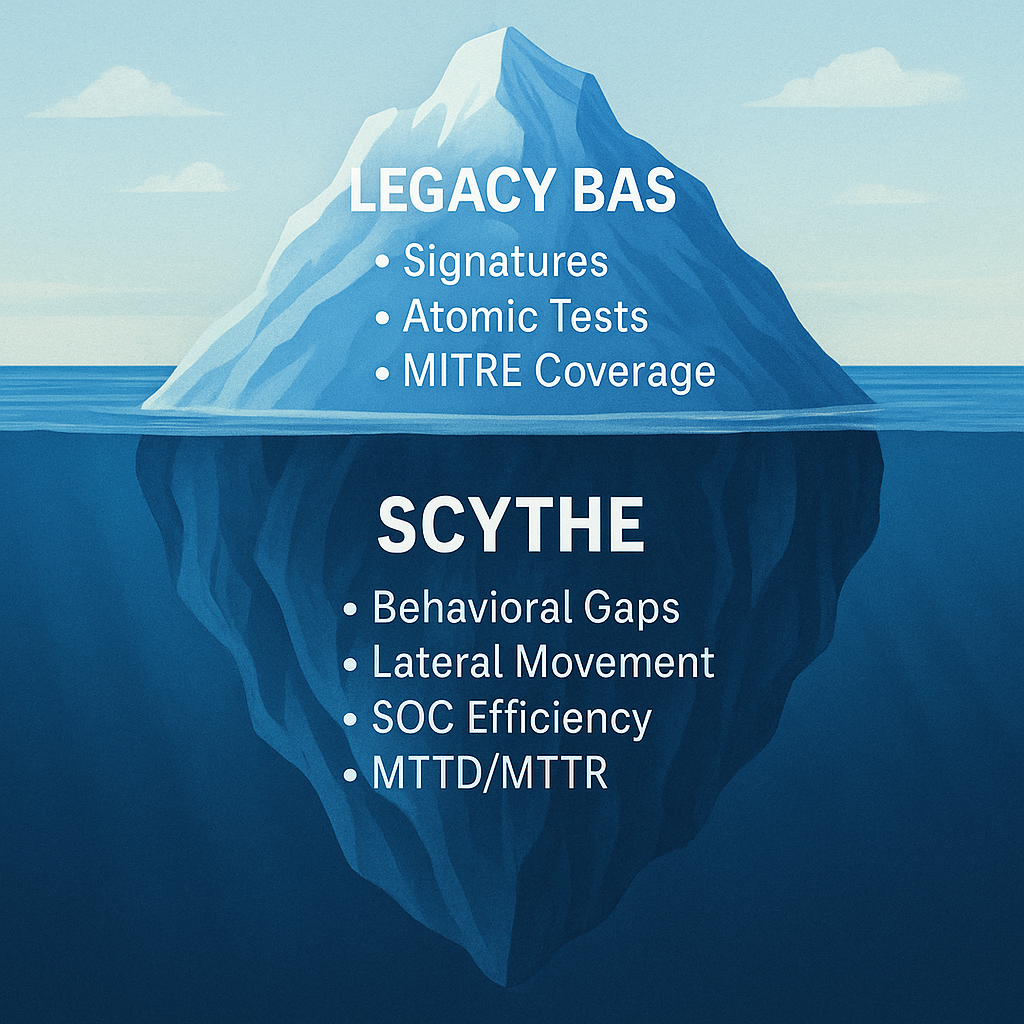
- Validate controls: How do you know the segmentation solution works? Sure, there is a firewall, but the any-any ruleset isn't helping. Conducting tactical or exercise-based purple teaming using threat-based thinking and procedures is a good way to build trust with O.T. and ensure security quality assurance that things work as expected. In addition, these processes meet TSA requirements for CAP, ADR, and CIRP assessments and provide continuous monitoring is working as designed.




.png)
.png)

