How MuddyWater Leveled Up Its Game.

TLDR: An Iranian state-sponsored hacking group silently attacked 18 organizations across Israel and Egypt between September 2024 and March 2025, stealing passwords, hijacking browser credentials, and digging into systems so quietly that traditional defenses barely blinked. If your organization touches government, telecom, tech, or critical infrastructure, this one's for you.
Picture this. Your IT team wraps up the annual pen test. The report comes back clean. Everyone breathes a little easier. Six weeks later, attackers are sitting inside your network, reading your files, copying your Chrome passwords, and quietly tunneling data out. No alarms. No red flags. Just silence. That is not a hypothetical. That is exactly what happened to 17 Israeli organizations and one Egyptian tech company over a six-month stretch ending in early 2025.
What's Happening
A hacking group known as Static Kitten (also called MuddyWater) has been running cyberattacks since at least 2017. Researchers at ESET confirmed this group operates under Iran's Ministry of Intelligence and Security. In December 2025, ESET published findings on the group's most refined campaign yet, code-named MuddyViper.
What makes this campaign different from past operations? The attackers got smarter. They moved away from noisy, obvious tactics and started operating like a ghost.
Why It Matters to You
This group does not care if you are not in the Middle East. Their target list keeps growing. They hit government agencies, telecom providers, defense contractors, and technology companies. If your organization connects with any of those sectors, you are potentially on the radar.
The most interesting part is that the tools they used in this campaign are custom-built, specifically designed to fool automated security scanners. One piece of malware literally mimics the old Snake video game to delay analysis. Your standard defenses may never flag it.
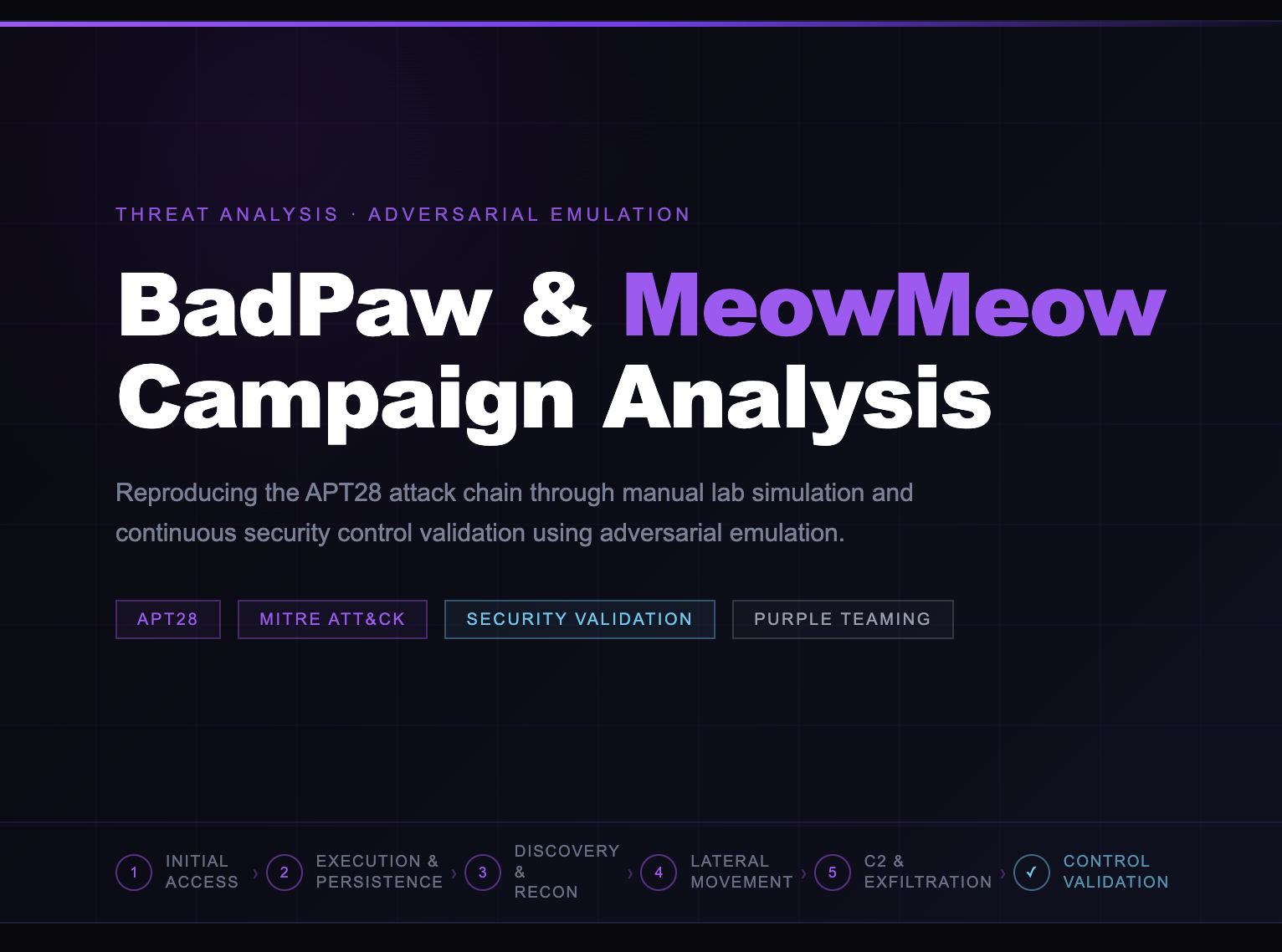
How It Works
The attack chain is impressive in a terrifying way. First, a custom loader drops onto the target machine and pauses, waiting to avoid triggering automated sandbox tools. Then it quietly establishes two separate ways to survive a reboot. It hides in your startup folder and creates a fake Windows scheduled task named something harmless like "ManageOnDriveUpdater."
Next, it grabs your credentials. It copies your Chrome password database and pulls login tokens from Windows system processes. Then it opens a secret communication tunnel out of your network, all while hiding its activity inside a trusted Windows process (svchost.exe) that most security tools trust by default. The attackers deliberately avoided typing commands interactively during the attack. Why? Because that kind of activity is noisy and easy to catch. These operators are disciplined and patient.
The Kicker
Your annual pen test would almost certainly miss this. Pen tests look for open doors. This threat walks in through a door that was technically closed, using stolen keys, and then quietly changes the locks from the inside.
That is the difference between knowing you have vulnerabilities and knowing whether your defenses work when a real adversary shows up. A point-in-time report does not catch a patient attacker who spent six months inside 17 organizations.
How We Help Our Customers Validate
We developed a SCYTHE Adversarial test that emulates the MuddyViper campaign's behaviors, allowing our customers to drive true threat signals in their environments, not just play the what-if game.
Our test will:
-
Deliver a 2-stage malware campaign emulating the MuddyViper campaign as reported by ESET.
-
Establishes persistence over multiple methods, including registry modification and scheduled tasks.
-
Collects Chrome extensions, credentials, and other DB entries.
-
Stands up a SOCKS5 tunnel to run an alternate C2 channel.
Your Action Plan
Do Today (5-15 minutes)
- Open your browser's password manager right now and remove any saved passwords for work accounts. Attackers specifically target Chrome credential databases.
- Search your scheduled tasks for anything named with words like "Update," "Manager," or "Cache" that your IT team did not create.
This Week (1-2 hours)
- Ask your IT team to confirm that endpoint detection tools are monitoring svchost.exe for unusual behavior, specifically instances that launch without the standard system arguments.
- Verify that the startup folder registry keys on Windows endpoints are set to approved default paths only.
This Month (Planning and policy)
- Schedule a conversation about Adversary Emulation Validation (AEV) for your organization. AEV uses automated threat emulation mapped to real attack groups, such as Static Kitten, giving you a continuous, real-world picture of how your defenses perform. Not a snapshot. Not a compliance checkbox. Actual proof.
- Review which employees have saved browser credentials for sensitive systems and set a policy requiring a password manager with MFA instead.
The Bottom Line
Static Kitten did not break down any doors. They slipped in quietly, worked patiently, and covered their tracks. The organizations they hit had security tools running. The tools just were not tested against this kind of real-world behavior. You do not have to accept that risk. Knowing your vulnerabilities is step one. Knowing your defenses stop a real attacker? That is confidence. And that is exactly what adversary emulation is built to give you. Want to know if your organization would catch Static Kitten in the act? Let's find out together.
Sources: ESET Research, "MuddyWater: Snakes by the Riverbank" (December 2025); SCYTHE Adversary Emulation documentation, Static Kitten/MuddyViper campaign analysis; Securelist