In most cases, ransomware is perceived as one threat with one attack type, but there are several attack types that end in ransomware deployment. Ransomware attacks come in different shapes, sizes, and capabilities. Therefore, there should be layers of various operational and tactical approaches to achieve the strategic goal of defending ransomware in its various attack chains and distribution methods. Defenders must understand their differences as the defensive strategies shift for each type.
The Worms
When people think of ransomware, they think of this type of attack. A worming attack chain is far less common. Nonetheless, people associate the worming type like WannaCry, which caused a global four-billion dollar estimated impact1 that made front-page headlines worldwide.
When it comes to worming ransomware, the attack self-replicates, spreading automatically from victim to victim, exploiting vulnerabilities or compromised credentials. These attacks are commonly thwarted by patching wormable exploits. Due to worming attack vector patching, the opportunity to conduct them is very limited. The current market price of a zero-click remote code execution exploit, like one needed for worming, can fetch over one million dollars, according to Zerodium.2 These types of capabilities are not easy to find, develop, or procure and are typically held for nation-states. Therefore, worming attack paths are far less common.
Spray & Pray
The spray and pray attacks are often associated with auto encryption and rely on weaknesses in public-facing systems or services. This method gains access to public-facing services via exploitation or default credentials. Once compromised, the system is encrypted, and no lateral movement is observed. This type has been recently observed in the ESXiArgs attacks,3 where the attackers exploited public-facing ESXi hosts and encrypted them.
These types of attacks are what are addressed when thinking of attack surface management. To defend them, organizations need to ensure there are no public-facing vulnerabilities, nor logins that are default or easily brute-forced.
Human-Operated Ransomware
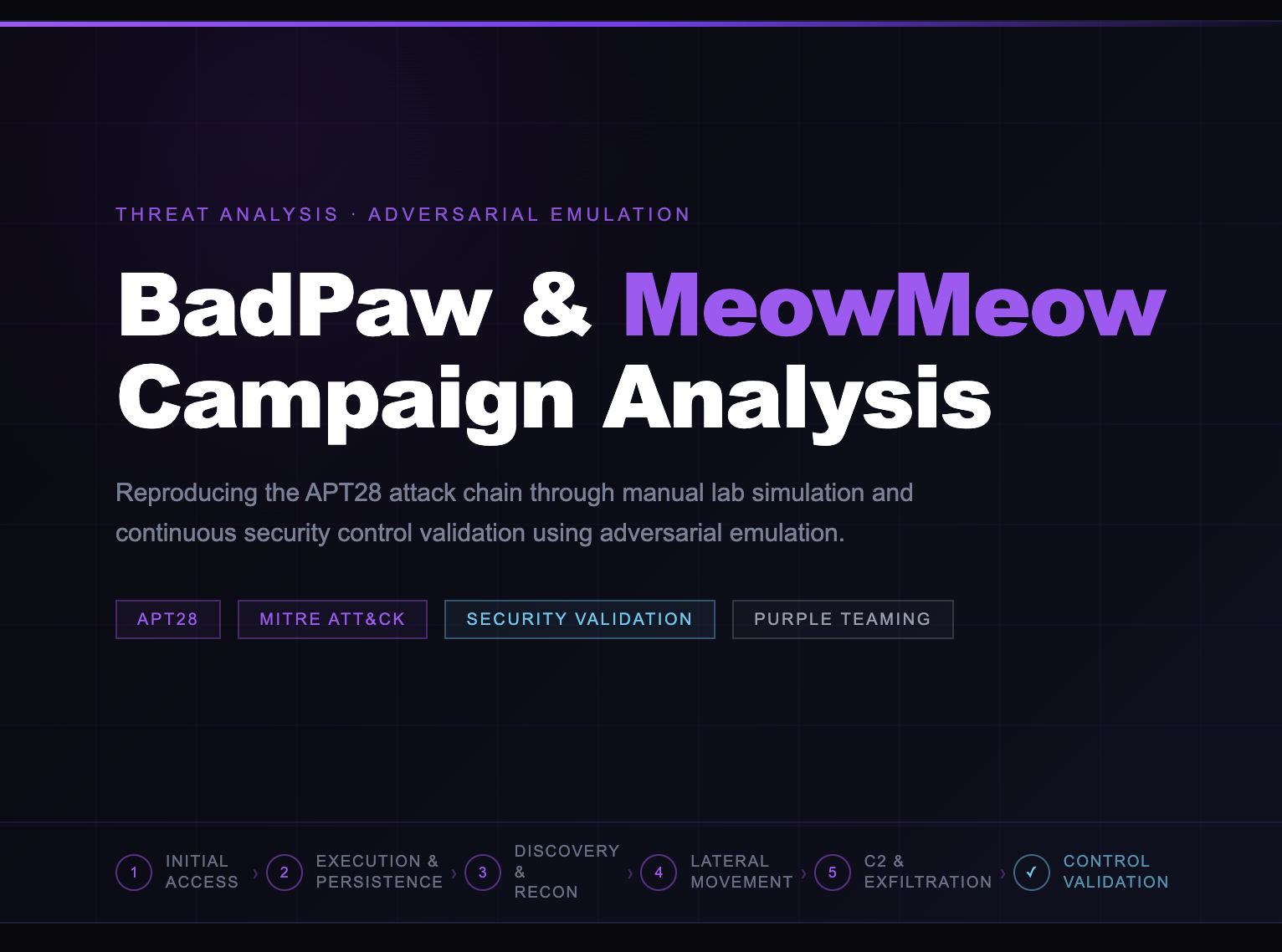
When compared to the other two vectors, human-operated ransomware is the hardest to defend against and is typically carried out by a group of human operators, instead of scripts, who manually move throughout a target’s networks and systems. Initial access is seen via a variety of tactics, including phishing, exploitation of public-facing applications, social engineering, and brute-force attacks, to gain access. Once in, the attackers blend into an environment by leveraging LOLBAS,4 injecting into legitimate processes, and using remote access software like TeamViewer, Atera, or Anydesk. After establishing persistence, attackers identify paths to high-value targets or seek domain admin credentials to deploy a ransomware payload to every system on the domain.
While all forms of ransomware can devastate organizations, human-operated ransomware is typically more challenging to detect and mitigate, as attackers are capable of evading traditional security measures. It's essential to have robust security measures that test and fix controls, alerting, and response deficiencies for known actions these human operators take. Human-operated ransomware can typically be caught and remediated before the deployment of ransomware, as the attack chains provide many detection opportunities.
Recently the Photon Research Team reported5 an incident where containment was achieved on the second day of activity after the adversary leveraged Netscan to enumerate file shares. Focusing on ransomware precursors was a highlight in Red Canary’s 2023 Threat Detection Report6 where they stated, “We focus on trying to detect ransomware precursor activity in the initial access, reconnaissance, and lateral movement phases and help our customers stop it before it gets to exfiltration or encryption. The result is that we see many more so-called ransomware precursors than we do actual ransomware payloads.”
For a complete six-day ransomware attack chain example, please see The DFIR Report’s Emotet Strikes Again writeup.7
SCYTHE Solution
Scythe has the world’s most extensive library of procedure-level ransomware emulation plans. This allows defenders to test their defenses and detections against procedures and their mapped techniques used by human-operated ransomware and tune or create alerts to catch them earlier in the attack chain. The purple team process also reduces the mean time to detect, contain, and remediate. Furthermore, SCYTHE offers tests for procedure variations to grow coverage of possible TTPs the adversaries may use in future attacks.
SCYTHE allows procedure-level intelligence to be actionable by testing alert capabilities in each unique security stack. SCYTHE’s data generation capability tests that the logging, alerting, and response meets the expectations of leadership and enables them to know where they stand.
References:
- https://www.cbsnews.com/news/wannacry-ransomware-attacks-wannacry-virus-losses/
- https://zerodium.com/program.html
- https://thehackernews.com/2023/02/esxiargs-ransomware-hits-over-500-new.html
- https://lolbas-project.github.io
- https://www.reliaquest.com/blog/qbot-black-basta-ransomware/
- https://resource.redcanary.com/rs/003-YRU-314/images/2023_ThreatDetectionReport_RedCanary.pdf
- https://thedfirreport.com/2022/11/28/emotet-strikes-again-lnk-file-leads-to-domain-wide-ransomware/