AEV vs. BAS vs. Penetration Testing
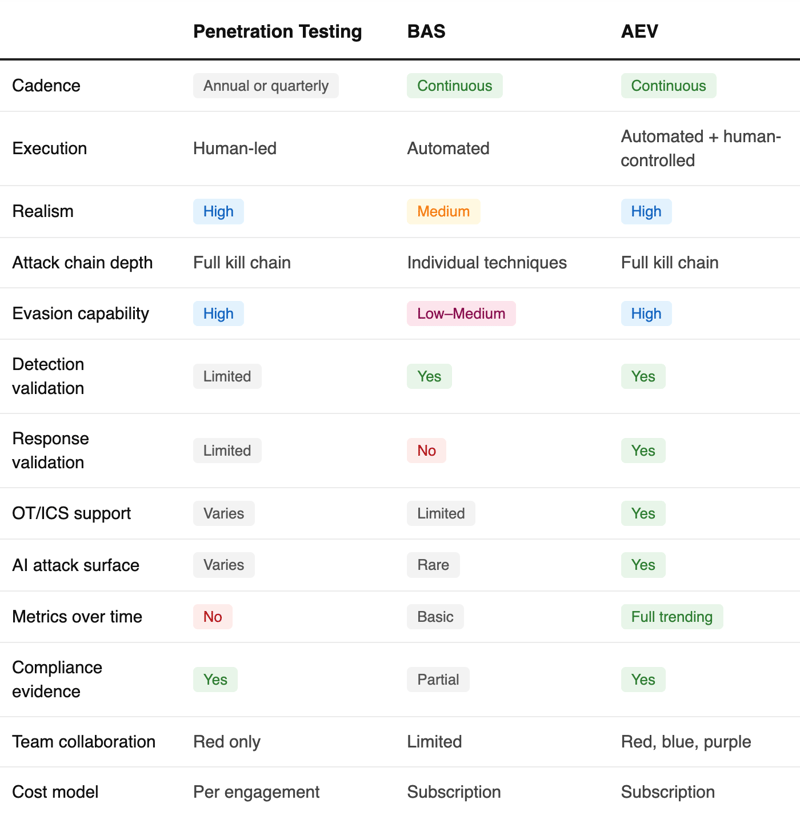
Security leaders today face a crowded market of testing methodologies, each claiming to validate defenses. Penetration testing, Breach and Attack Simulation (BAS), and Adversarial Exposure Validation (AEV) are frequently mentioned in the same breath — but they solve fundamentally different problems, operate at different cadences, and produce different kinds of evidence.
This page explains what each approach actually does, where each one falls short on its own, and how forward-thinking organizations are combining them into a continuous validation program.
The Core Problem All Three Try to Solve
Every security team makes assumptions. Assumptions that the EDR catches lateral movement. That the SIEM fires an alert when credentials are dumped. That the firewall blocks command-and-control traffic. That the incident response playbook works under real pressure.
The question isn't whether your security controls are configured — it's whether they actually work against the adversaries targeting your organization right now. That's the question penetration testing, BAS, and AEV each attempt to answer, in very different ways.
Penetration Testing: Deep but Point-in-Time
A penetration test is a time-boxed engagement — typically one to four weeks — where skilled professionals attempt to breach your environment using real attacker techniques.
Where it excels
- Uncovers exploitable vulnerabilities with human creativity and judgment
- Satisfies compliance mandates (PCI DSS, SOC 2, ISO 27001)
- Reveals complex, chained attack paths automated tools miss
Where it falls short
- Results are valid for the day the test ended — not months later
- Can't tell you whether your detections fired, only whether someone got in
- No continuous coverage — cost and logistics prevent it
When it's the right choice
Pre-launch assessments, compliance obligations, deep application reviews, and complex attack path analysis. Penetration testing is essential — but it's not a substitute for continuous validation.
Breach & Attack Simulation: Automated but Limited in Depth
BAS platforms automate the execution of known attack techniques — typically mapped to MITRE ATT&CK — to continuously test whether your controls detect or block them.
Where it excels
- Runs continuously without requiring human testers
- Maps results to MITRE ATT&CK for standardized reporting
- Identifies detection gaps at scale across endpoint, network, and email
Where it falls short
- Tests techniques in isolation — not realistic multi-stage attack chains
- Static, script-based logic doesn't reflect how real adversaries operate
- Shows whether an alert fired, not whether anyone responded correctly
When it's the right choice
Organizations needing continuous coverage of a defined technique library across a stable environment. BAS works best as a baseline measurement tool — not a realistic adversary simulation.
Adversarial Exposure Validation: Always On, Real, and Proven
AEV is the evolution of security testing — combining the realism of penetration testing with the automation of BAS, plus the measurement infrastructure to track improvement over time.
Where it excels
- Emulates real adversary behavior across the full kill chain — not isolated techniques
- Runs continuously after every tool change, config update, or rule modification
- Measures detection and response, not just prevention — validating alerts fire and SOC workflows trigger
- Tracks quantified metrics over time: detection coverage, MTTD, MTTR
Where it's the right fit
Organizations that have moved past "do our controls exist?" and are asking "do they actually work — and how do we prove it?" AEV turns security testing from an annual event into a continuous program.
The SOC Investment Gap
Pen Testing Validates Getting In. It Ignores What Happens Next.
The most mature security programs don't choose between penetration testing, BAS, and AEV, they use each for what it does best.
The Bryson Attack Model (BAM™) makes the structural limitation of penetration testing visible. Testing effort concentrates at Recon and Initial Access — the left side of the kill chain. But the right side is exactly where your security investments live: SIEM rules, EDR policies, detection playbooks, SOC workflows and your team.


This is why AEV and penetration testing are complementary, not competing. Pen testing remains the right tool for deep application reviews, compliance obligations, and finding novel attack paths. AEV provides the continuous validation layer that proves your detections hold — and measures your SOC's response across the full kill chain, on a cadence that matches how fast your environment changes.
Adversarial Exposure Validation
These Approaches Are Complementary, Not Competing
The most mature security programs don't choose between penetration testing, BAS, and AEV, they use each for what it does best.
Penetration testing handles annual compliance obligations, pre-launch assessments, and deep application security reviews where human creativity and judgment are irreplaceable. AEV runs continuously in the background, validating controls after every change, ensuring red team findings are re-tested automatically, and generating the ongoing evidence of effectiveness that leadership and auditors need. But only dynamic AEV delivers on that promise. Static, script-based simulations produce repeatable noise; real adversaries don't follow scripts, and neither should your validation.
That realism is what makes AEV useful for measuring the human layer, not just the technology stack.
MTTR isn't only a tool metric. It tells you whether your analysts caught it, how fast they responded, and whether your team has the training and capacity to act. A detection that fires but sits unresolved for 72 hours surfaces something no control report will: a resourcing or readiness gap that better tooling alone won't fix.
The result is a program that catches what point-in-time testing misses and gives every stakeholder — from the SOC analyst to the board — the full picture: not just are the tools on, but can the team actually defend us.
How SCYTHE Operationalizes AEV
SCYTHE is the leading Adversarial Exposure Validation platform, purpose-built for organizations that need continuous, realistic security control validation across IT, cloud, OT, and AI-enabled environments.
Unlike traditional BAS tools that test techniques in isolation, SCYTHE emulates real adversary campaigns — multi-stage, evasive, and mapped directly to MITRE ATT&CK — and validates that your entire detection and response chain works, not just that individual alerts fire.
Key outcomes organizations achieve with SCYTHE:
- 4× increase in continuously executed detection tests
- 80%+ automation of routine validation
- 25–60% improvement in detection coverage
- 30–50% reduction in false negatives
- 60%+ reduction in detection MTTR
Ready to see continuous validation in action?
Book a personalized SCYTHE demo and see how AEV turns security testing from a point-in-time exercise into a continuous program.
Contact Us
Contact Us
Frequently Asked Questions
Is AEV the same as BAS?
Can AEV replace penetration testing?
Does SCYTHE replace our red team?
What is Continuous Threat Exposure Management (CTEM) and how does AEV fit?
How long does it take to see results with AEV?
Latest Blogs
Contact Us
Welcome to SCYTHE, your partner in understanding and defending against cyber attacks. We appreciate your interest in enhancing your cybersecurity defenses.
Please fill the form to reach out to our dedicated team.