CTEM · Phase 4 · Validation
CONTINUOUS THREAT EXPOSURE MANAGEMENT
CTEM Programs fail at Validation. SCYTHE fixes that.
Most organizations have a CTEM framework. Few have solved Phase 4 — the continuous, production-safe adversary emulation that turns five-phase theory into measurable security improvement.
| Book a Demo See How Validation Works |
THE CTEM FRAMEWORK
Five Phases. One Consistently Unsolved.
Gartner's CTEM framework gives security programs a clear structure. But Phase 4 — Validation — is where most programs stall. It's the only phase that requires actually running adversary techniques against your live environment.
|
01
Scoping
Define what you're protecting and which threat actors are relevant. A strategic planning exercise driven by business priorities. Solved by: Risk frameworks, threat intel programs, CISO-level scoping |
02
Discovery
Identify assets, vulnerabilities, and exposures within scope using scanners, ASM tools, and configuration review. Solved by: Vulnerability scanners, ASM platforms, CSPM tools |
03
Prioritization
Rank exposures by exploitability and business impact. Effective prioritization depends on validation evidence — which most teams don't yet have. Solved by: Risk scoring tools, threat intel — fed by Phase 4 ↑ SCYTHE validation evidence improves prioritization accuracy |
⚡ Where SCYTHE Lives
04
Validation
Prove — with evidence — that an exposure is real and exploitable, and that your security controls either detect or miss the exploitation attempt. Requires actually running adversary techniques against your live environment, continuously, at scale. Solved by: SCYTHE — continuous adversary emulation, production-safe, ATT&CK-mapped, scheduled or change-triggered |
05
Mobilization
Turn validated findings into remediation tickets and detection improvements. SCYTHE initiates this loop via SOAR and ITSM integrations. Executed by: Your SOAR, ITSM, and detection engineering workflows ↑ SCYTHE pushes validated findings into your ticketing pipeline |
WHAT SCYTHE DELIVERS
Three Things Continuous Validation Produces.
SCYTHE operationalizes Phase 4 specifically — providing the evidence that feeds Phases 3 and 5 and keeps your CTEM program running continuously.
|
🎯
Validated Prioritization Evidence
Not "this CVE scores 9.1" — but "this adversary technique executed in your environment without detection." SCYTHE produces the exploitability evidence that makes Phase 3 prioritization defensible and accurate. ATT&CK Coverage Map False Negative Rate Exploitability Evidence
|
🔄
Continuous Testing Cadence
Scheduled daily or weekly, and automatically re-triggered by any change event — agent upgrade, policy change, new system in scope. Every change is a potential regression. SCYTHE finds them before attackers do. Scheduled Runs Change-Triggered Testing Regression Detection
|
🔗
Closed-Loop Mobilization Triggers
Validated findings flow directly into ServiceNow, Jira, or your SOAR platform — with ATT&CK context and evidence attached. SCYTHE starts Phase 5; your existing workflows complete it. SOAR Integration ITSM Ticketing <48h Analysis & Re-test Cycle
|
THE SOLUTION
How SCYTHE Runs Phase 4
|
Continuous Testing at Production Scale
|
||
|
SCYTHE runs validation tests automatically on a configured schedule — daily, weekly, or triggered by change events — so you always have a current picture of your detection coverage, not a point-in-time snapshot from your last red team engagement. |
||
|
||
|
||
|
||
| CrowdStrike Falcon Microsoft Defender SentinelOne Cortex XDR Carbon Black |
|
Full Response Chain Validation
|
||
|
SCYTHE doesn't just test whether the EDR detects a technique — it validates the entire downstream chain. A detection that fires but produces no actionable alert is not a working detection. |
||
|
||
|
||
|
||
| Splunk Microsoft Sentinel Elastic SIEM IBM QRadar Chronicle |
|
Regression Testing After Changes
|
||
|
Every OS update, EDR agent upgrade, detection policy change, or new system entering scope is a potential regression event. Without continuous testing, you won't know until an attacker finds the gap first. |
||
|
||
|
||
|
||
| Policy Change Triggers Agent Upgrade Triggers New System Scope Full Audit Trail |
HONEST POSITIONING
Where SCYTHE Fits — and Where It Doesn't.
A complete CTEM program needs more than one tool. Here's what SCYTHE does, what it feeds, and what you'll need alongside it.
SCYTHE is purpose-built for Phase 4 Validation — the hardest and most commonly skipped phase of CTEM. It also produces evidence that materially improves Phases 3 and 5.
The other phases are well-served by existing tools your team likely already has. SCYTHE integrates with them — it doesn't replace them.
|
You'll use alongside SCYTHE:
|
||
|
||
|
||
|
||
|
Buyers who trust a vendor enough to hear what it doesn't do are more likely to become long-term customers. SCYTHE solves the hardest phase — and integrates cleanly with everything else. |
|
|||||||||
|
|||||||||
|
|||||||||
|
|||||||||
|
THE BUSINESS CASE
What Phase 4 Validation Produces.
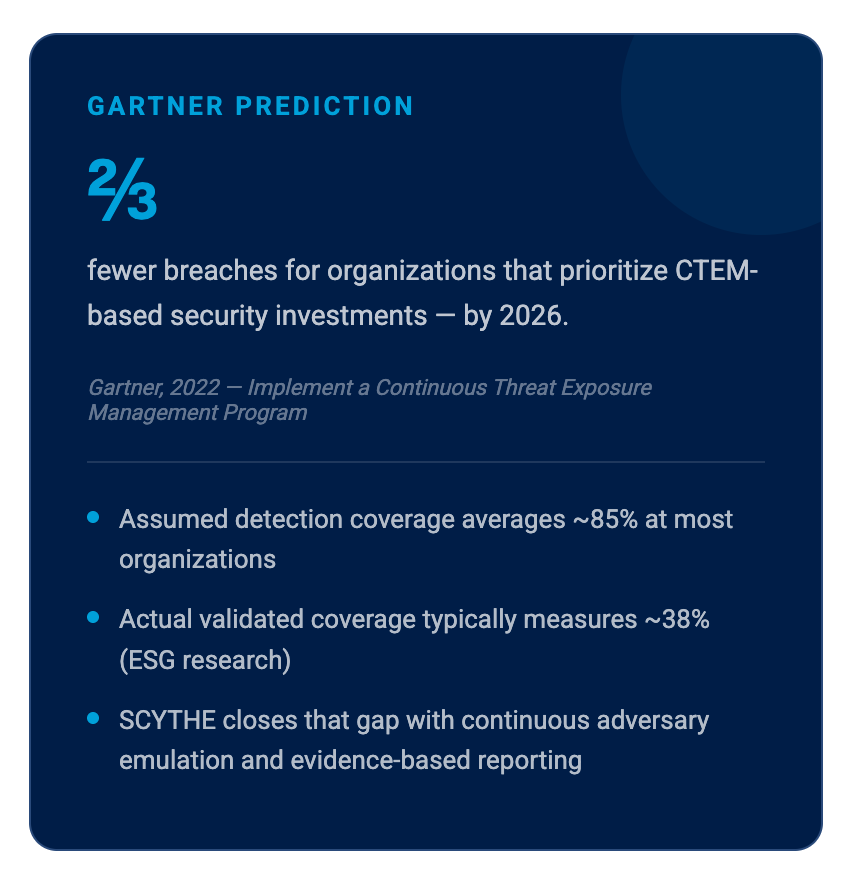
Continuous validation turns assumptions into evidence. Based on customer-reported outcomes.
|
3×
reduced breach risk
|
50%
improvement in remediation velocity
|
38%+
improvement in ROI linkage to investments
|
COMMON QUESTIONS
Frequently asked questions
Why does CTEM fail at Phase 4 specifically?
Is SCYTHE safe to run in a production environment?
How is SCYTHE different from Atomic Red Team or other open-source tools?
Do we need a dedicated red team to use SCYTHE for CTEM?
How quickly will we see results after deployment?
Solve the Phase Your CTEM Program Is Skipping.
Book a 30-minute demo. We'll run a live validation campaign and show you your actual ATT&CK coverage, false negative rate, and first regression risk areas, the evidence your CTEM program needs to function.