
Best Breach and Attack Simulation (BAS) & AEV Tools 2026
Updated April 2026 Reviewed by the SCYTHE team, the platform built for adversary emulation and AEV
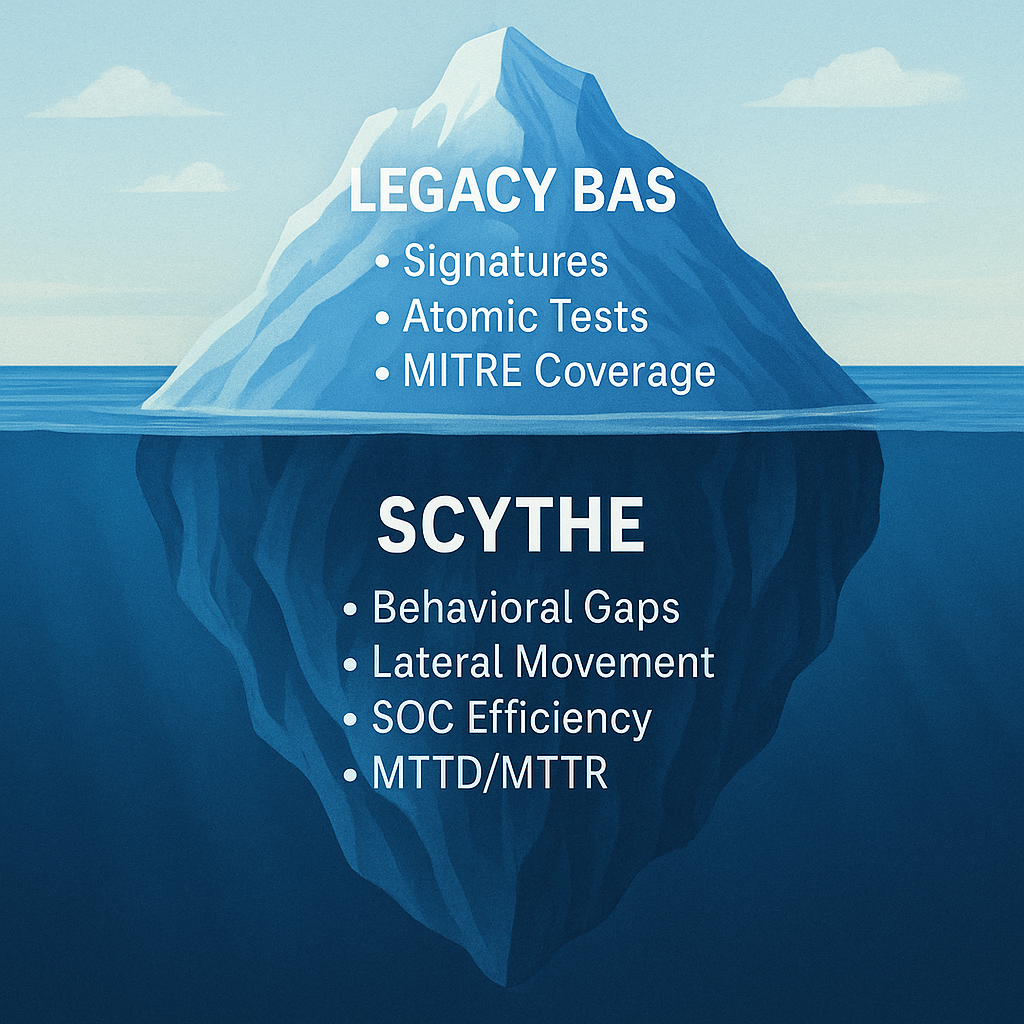
SCYTHEBreach and Attack Simulation (BAS) tools emerged to solve a real problem: security teams were spending heavily on controls they had never tested against real adversary behavior. BAS automated that testing. But the category has moved. In 2024, Gartner introduced Adversarial Exposure Validation (AEV), a broader framework that encompasses continuous, multi-stage adversary emulation across the full kill chain, not just isolated technique checks.
The ten platforms on this list span that spectrum, from foundational BAS BAS to full AEV. Knowing where each fits matters before you evaluate. This list is maintained by the SCYTHE team. We are included on it. We've noted that clearly in our entry and throughout the comparison.
|
What's the difference between BAS and AEV?
BAS tools validate that security controls block or detect specific techniques, typically in isolation. AEV goes further: it emulates realistic multi-stage adversary campaigns in your live environment and validates the full response chain, from technique execution through EDR detection, SIEM alerting, and SOC response action. AEV vs. BAS vs. Penetration Testing: Full breakdown → |
How we selected these tools
Platforms were evaluated across five dimensions: depth of adversary emulation (simulation vs. true emulation), campaign fidelity (atomic tests vs. multi-stage kill chain), environment coverage (IT, cloud, OT/ICS, air-gapped), response chain validation depth (EDR-only vs. SIEM + SOC workflow), and continuous vs. point-in-time testing. Pricing, customer reviews, and third-party analyst coverage were also considered. Entries are based on publicly available information and customer research as of April 2026.
SCYTHE is the platform behind this list. We're disclosing that upfront. We've included ourselves because we believe the comparison is honest, and because the capability differences between AEV and legacy BAS matter to anyone making a buying decision.
SCYTHE is a continuous Adversarial Exposure Validation platform that emulates real adversary behavior, not simulated approximations, against your live production stack. Where most BAS tools ask "did the EDR fire?", SCYTHE validates the entire response chain: technique executed → EDR detected → SIEM alert generated → SOC workflow triggered → response action completed. Every step. Every cycle. Continuously.
Campaigns are built from named threat actors, CISA advisories, or plain-language descriptions, with AI-assisted generation and a mandatory human approval gate before anything runs. SCYTHE is the only AEV platform purpose-built for both IT and OT/ICS environments, supporting air-gapped and on-premises deployment for critical infrastructure, energy, defense, and manufacturing.
Cymulate is one of the most widely deployed BAS platforms in the enterprise market, known for its breadth of coverage across attack surfaces and its accessible SaaS delivery model. The platform runs continuous attack simulations across email security, web gateway, data exfiltration, lateral movement, and endpoint vectors, giving security teams a broad view of which controls are working and which aren't.
Cymulate's strengths are its ease of deployment, its rich library of out-of-the-box scenarios, and its ability to surface remediation priorities quickly. It is primarily prevention-focused: most testing validates whether controls block or detect techniques at the control layer, rather than tracing outcomes through the full SOC response chain.
AttackIQ is one of the original BAS platforms and remains closely associated with the MITRE ATT&CK framework. The company was a founding partner of the Center for Threat-Informed Defense (CTID). Its Security Optimization Platform lets security teams run automated attack scenarios mapped to MITRE ATT&CK tactics, techniques, and procedures, validating detection and prevention controls against a broad library of threat scenarios.
AttackIQ's managed offering, AttackIQ Ready!, lowers the operational bar for organizations without dedicated red team resources. The platform is predominantly focused on technique-level testing. It excels at measuring ATT&CK coverage but is less focused on validating SOC response workflows or multi-stage campaign behavior.
SafeBreach is one of the BAS category pioneers, with one of the largest breach simulation playbook libraries in the market. The platform continuously runs attack simulations across your environment, covering infiltration, lateral movement, and exfiltration scenarios, and surfaces risk from the attacker's perspective. SafeBreach focuses on showing where defenses succeed and fail across the full attack lifecycle.
SafeBreach's simulator-based approach means it can run safely across production environments without requiring agents on every endpoint. The platform's reporting is strong for communicating risk posture to leadership, though it is primarily simulation-based rather than true behavioral emulation.
Picus Security's Complete Security Validation Platform combines BAS, automated penetration testing, and exposure validation into a single offering. The platform is particularly well regarded for its remediation guidance: Picus provides vendor-specific mitigation recommendations, telling security teams not just that a gap exists but exactly how to tune their existing tools to close it.
Picus maintains a large and frequently updated threat library, with attack content typically available within 24 hours of new threat actor activity being identified. Its Exposure Validation module extends coverage beyond prevention testing into broader attack surface assessment. Like most BAS platforms, it is primarily focused on prevention-gap identification rather than full SOC response chain validation.
XM Cyber takes a distinct approach within this category. Rather than focusing on technique execution and control validation, it specializes in continuous attack path analysis. The platform models how an attacker could chain vulnerabilities, misconfigurations, and identity exposures together to reach critical assets, then prioritizes remediation by attack path impact rather than generic severity scores.
XM Cyber is acquired by Schwarz Group and has strong presence in hybrid on-premises and cloud environments. Its differentiation is in exposure prioritization and architectural security analysis, making it more of an attack surface management tool with simulation capabilities than a traditional BAS or AEV platform.
Pentera (formerly Pcysys) occupies the space between BAS and automated penetration testing. Its platform actively attempts to exploit vulnerabilities in your environment, not just simulate the attempt. This gives it more realistic attack outcomes than most BAS tools, but also means it requires more careful scoping and change management before running in production environments.
Pentera's output reads more like a traditional pen test report, with prioritized findings and exploit evidence, making it useful for organizations that need pen test-style deliverables on a continuous automated schedule. It is less focused on team collaboration workflows (purple teaming) or SOC response chain validation than AEV-oriented platforms.
Mandiant Security Validation (now part of Google Cloud Security) leverages Mandiant's deep threat intelligence library to drive BAS content. The platform allows organizations to test defenses against attack scenarios built directly from Mandiant's frontline incident response data, a meaningful differentiator for teams that want simulations grounded in current, observed adversary behavior rather than generic playbooks.
The platform integrates with Google Security Operations (Chronicle) for teams already in the Google ecosystem. Its depth of threat intelligence is a genuine strength, though the platform's roadmap and positioning within Google's broader portfolio continues to evolve since the Mandiant acquisition.
Randori, acquired by IBM Security, combines external attack surface management with automated attack simulation, presenting what's visible and exploitable from an outside attacker's perspective. Its "hacker's-eye view" approach starts with continuous discovery of internet-exposed assets, then automatically identifies and prioritizes targets based on their attractiveness to a real attacker.
Randori integrates with IBM Security QRadar for organizations already in the IBM ecosystem. Its differentiation is external-first visibility. It excels at finding what you've forgotten exists on the internet before an attacker does. For internal network validation and detection engineering, organizations typically pair it with a complementary BAS or AEV platform.
OpenAEV is Filigran's open-source adversarial exposure validation platform, part of the same ecosystem as OpenCTI, the widely deployed open-source threat intelligence platform. Filigran's approach connects threat intelligence directly to simulation: CTI from OpenCTI flows into OpenAEV to generate attack scenarios based on observed adversary behavior, giving teams a tightly integrated intelligence-to-validation pipeline.
As an open-source platform, OpenAEV is well suited for teams with engineering capacity to deploy, configure, and extend it, and for organizations where total cost of ownership and vendor independence are priorities. Enterprise support and managed options are available through Filigran. Teams already running OpenCTI will find the integration especially compelling.
BAS vs. AEV: Which does your program need?
Most of the platforms on this list are BAS tools: they simulate attacks to validate whether controls are configured to block or detect specific techniques. That's useful. But it answers a narrower question than AEV does.
AEV asks: when a real adversary runs a real technique in your real environment, does the full response chain work, from detection through alerting through SOC response, or does something break? That's a different question. And the answer is almost always different from what teams assume.
|
The most mature security programs don't choose between BAS and AEV. They use BAS for broad control coverage measurement and AEV for continuous, production-validated assurance that the full response chain actually works. AEV vs. BAS vs. Penetration Testing: full comparison → |
|
Ready to go beyond BAS?
See what AEV finds that BAS misses.Most teams discover response chain gaps during an incident, not during a BAS test. A SCYTHE demo runs a live emulation against a technique relevant to your industry and shows exactly where detection, alerting, or SOC response breaks down. Before an attacker finds out first. |
Latest Posts
Related Articles


Florida Water Plant Breach
TeamViewer was at the forefront of an attack on a Florida water facility in February 2021. A...
Measuring Cyber Risk with Bryson Bort & Paul Rosenzweig
Good management of cyberspace requires a system of cyber metrics that are transparent, auditable,...

.png)
.png)