Opinion Controls Validation Detection Engineering Purple Teaming
A determined adversary will get in. The question that actually matters is whether your people, processes, and technology can detect what they do next — and contain it before business impact.
SCYTHE · Updated April 2026 · 10 min read
82%
Of breaches involve post-access techniques
10 days
Avg. dwell time before detection
56%
Of post-access behaviors go undetected
100%
Of ransomware impact occurs post-breach
There's a moment in every purple team planning meeting, every workshop, every demo, where someone asks: Why should we click on this? Wouldn't our firewall, our EDR, our user training have stopped this from executing?
It's a fair question. And the answer is always the same: prevention has its place, but a determined adversary will achieve access eventually. The phishing email will get through. The zero-day will land. The compromised credential will work. The insider will plug in the device. What separates organizations that survive a breach from those that make headlines isn't whether they prevented initial access — it's whether they detected what happened next.
This is why SCYTHE was built on an assumed breach model. Not because prevention doesn't matter, but because the behaviors that cause business impact — privilege escalation, lateral movement, data staging, exfiltration, encryption for ransom — happen after the adversary is already inside. And those are the behaviors most organizations are least prepared to detect.
The Core Principle
Assumed breach shifts the question from "can we keep them out?" to "when they get in, can we detect what they do, contain the damage, and recover before business impact?" That shift changes everything — how you test, how you train, and how you measure security effectiveness.
The Problem with Prevention-First Thinking
Organizations that anchor their security programs to prevention spend the majority of their resources trying to stop initial access. Firewalls, email gateways, user awareness training, application whitelisting — all important, all necessary, and all insufficient against a motivated adversary with time, resources, and creativity.
Initial access is a point in time and a continuously moving target. New vulnerabilities emerge weekly. AI-generated phishing has made social engineering more convincing and harder to train against. Supply chain compromises bypass perimeter controls entirely. And every organization has employees whose jobs require interacting with external entities — opening documents, clicking links, reviewing files from vendors and partners.
When prevention fails — and it will — the organization's survival depends entirely on what happens in the next minutes, hours, and days. Can the SOC detect the adversary's post-access behavior? Can the IR team contain the spread? Can leadership make informed decisions based on real-time intelligence about what's been compromised? These are the questions that assumed breach forces you to answer before the real thing happens.
Five Scenarios Where Assumed Breach Changes Everything
Every organization faces scenarios where initial access is essentially inevitable. Here's how assumed breach reframes each one from a prevention problem into a detection and response opportunity.
Scenario 1
Social Engineering & Phishing
AI-powered phishing has fundamentally changed this threat. Adversaries now generate hyper-personalized lures, craft convincing voice calls, and impersonate colleagues with startling accuracy. Even security-conscious employees, facing a determined adversary who has researched their role and communication patterns, will eventually open something they shouldn't.
Assumed breach reframe: Stop blaming individuals for clicking a link. Start validating whether your EDR detects the payload execution, whether your SIEM alerts on the spawned process tree, and whether your SOC's response playbook contains the threat before lateral movement begins. The click is inevitable. Detection is the variable you control.
Scenario 2
Zero-Day & N-Day Exploitation
Every time a critical vulnerability drops — MOVEit, CitrixBleed, Ivanti, the next one we haven't named yet — leadership asks the same question: Are we exposed? The reality is that zero-day exploitation in the wild is accelerating, with state-sponsored groups and ransomware operators racing to weaponize new CVEs within hours of disclosure.
Assumed breach reframe: You can't prevent exploitation of a vulnerability you don't know about yet. But you can validate that your stack detects the post-exploitation behaviors that follow — credential dumping, persistence installation, lateral movement via RDP or SMB. Every zero-day follows a known post-access playbook. Test for that playbook today.
Scenario 3
Insider Threat
The insider threat spectrum ranges from a malicious actor deliberately exfiltrating data to an employee unknowingly plugging in a compromised USB drive. In both cases, the adversary already has access — there is no perimeter to defend. Detection depends on identifying anomalous behaviors: unusual data access patterns, unexpected process execution, off-hours lateral movement.
Assumed breach reframe: Insider scenarios are assumed breach by definition. The question is never "how did they get in" — they were already in. The question is whether your detection engineering catches the behaviors that distinguish normal employee activity from data staging, unauthorized access escalation, and exfiltration.
Scenario 4
You May Already Be Breached
Supply chain compromises, pre-installed backdoors, long-dwell APT campaigns — the uncomfortable truth is that some organizations are already compromised and don't know it. The SolarWinds attack demonstrated that even sophisticated security teams can harbor adversary access for months. With dwell times still averaging days to weeks in many industries, this scenario isn't hypothetical.
Assumed breach reframe: Regardless of how the compromise occurred, focus on what can be done now. Build situational awareness through increased telemetry and logging. Tune detection to your specific environment. Run adversary emulation campaigns that mirror known threat actor post-access playbooks and see whether your existing tooling catches them. If it doesn't, you've found the gap before the adversary exploits it.
Scenario 5
Business Impact Happens After the Breach
Ransomware remains the most visible proof of this principle. Double-extortion and triple-extortion groups now combine data theft, encryption, and public exposure into a single campaign. But the encryption event that locks systems and triggers crisis response is the last step in a chain that includes initial access, credential harvesting, lateral movement across the network, data staging, and exfiltration — all of which happen before the ransom note appears. Every one of those pre-impact behaviors is detectable.
Assumed breach reframe: If you detect the adversary at the lateral movement or data staging phase, you can contain the incident before ransomware deploys. The window between initial access and impact is where detection engineering earns its ROI. Validate that your stack catches the pre-impact behaviors by emulating them — repeatedly, continuously, against every change in your environment.
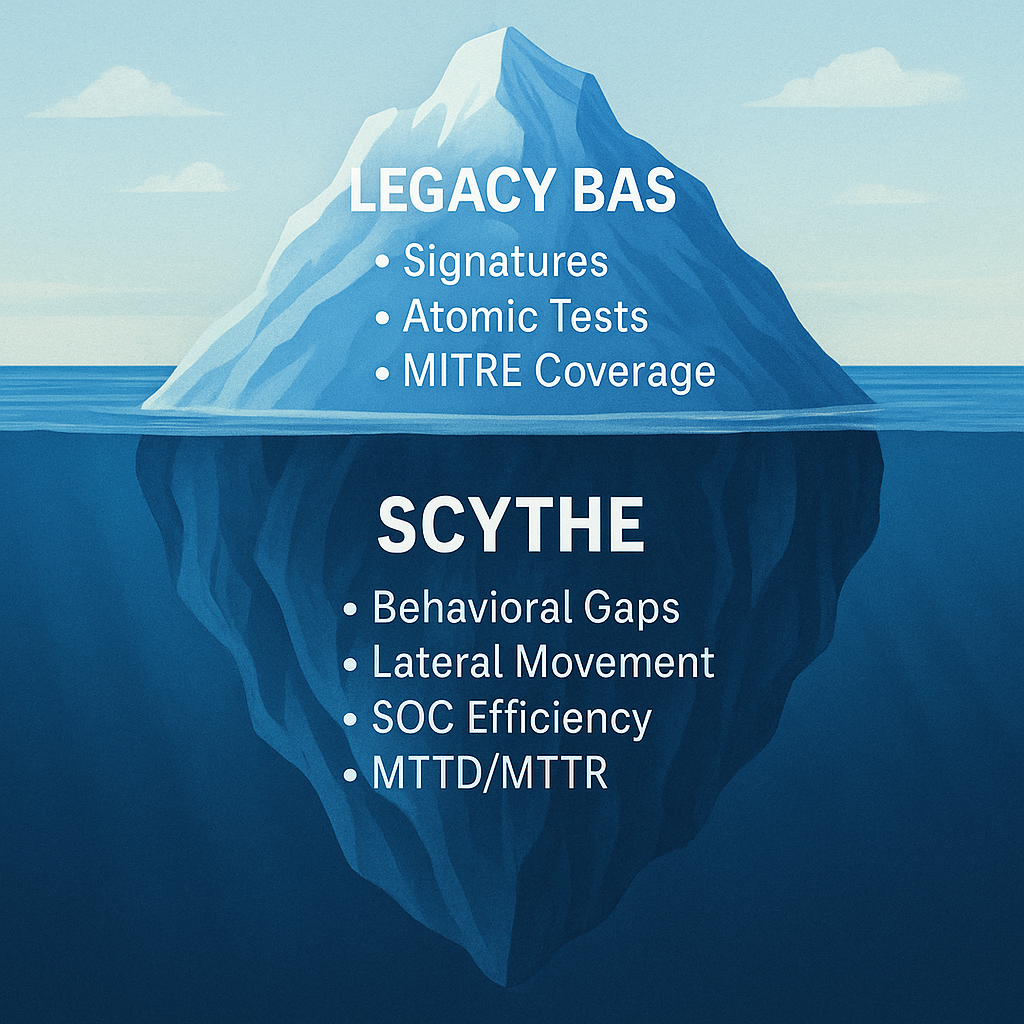
Why SCYTHE Was Architected for Assumed Breach
SCYTHE's platform was designed from the ground up around this principle. Every architectural decision — the agent-based implant model, the modular TTP library, the full kill-chain campaign execution, the agentless delivery options — reflects a belief that security validation starts after initial access, not before it.
When you run a SCYTHE campaign, you're not testing whether your firewall blocks a known-bad IP. You're testing whether your entire defensive stack — EDR, SIEM, SOC analysts, IR playbooks — can detect and respond to the execution, persistence, privilege escalation, lateral movement, and exfiltration behaviors that real adversaries perform after they're already inside your network.
This is also why SCYTHE supports deploying both cloud-hosted and on-premise servers behind your DMZ — to emulate adversaries operating from external C2 infrastructure as well as insiders or supply chain compromises operating from within the network perimeter. The flexibility to test both models is essential for realistic assumed breach validation.
Detection Is the Variable You Control
The recurring theme across all five scenarios is the same: move past initial access and focus on the harder, more consequential questions. How quickly can your team detect post-access behaviors? What is your response playbook? Can your technology contain the spread before it reaches critical assets?
Assumed breach doesn't mean giving up on prevention. It means acknowledging that prevention is a single layer — and building the detection, response, and containment capabilities that determine whether a breach becomes a headline or a closed ticket.
The adversary's advantage is getting in. Your advantage is knowing what they'll do next — and validating, continuously, that your people, processes, and technology can stop it.
Validate Your Post-Access Detection
Start With Assumed Breach. Prove Your Defenses Work.
SCYTHE gives red, blue, and purple teams the platform to emulate real-world adversary behaviors from the point of initial access through objective completion — and measure whether your security stack detects every step. With 1,400+ pre-built campaigns mapped to MITRE ATT&CK and support for both cloud and on-premise deployment, your team can go from assumed breach scenario to validated detection posture in hours.
Explore the post-access kill chain with our eBook: Transforming Cyber Defense Through Adversarial Behavior Detection
Schedule a Demo

.png)

.png)
.png?width=352&name=5ff7686c781a6fbae8901c7f_Red%20Team%2010%20(5).png)