Blog Red Teaming Controls Validation Purple Teaming
You bought the tools. You hired the team. You passed the audit. But can your defenses actually stop a real adversary? The only way to know is to emulate one.
SCYTHE · Updated April 2026 · 12 min read
Most security programs are built on assumptions. You assume the EDR is configured correctly because you deployed it. You assume the SIEM rules fire because you wrote them. You assume the SOC would detect lateral movement because they attended the training. You assume the IR playbook works because it was approved.
Adversary emulation replaces assumptions with evidence. It's the practice of executing real-world adversary behaviors — mapped to MITRE ATT&CK, informed by threat intelligence, and tailored to your environment — against your production defenses to see what actually gets detected, what gets blocked, and what sails through unnoticed.
In 2026, with AI-accelerated threats compressing the time between vulnerability disclosure and weaponized exploit, with CTEM programs requiring continuous validation, and with boards demanding evidence that security investments deliver measurable outcomes — adversary emulation isn't optional. It's how modern security programs prove they work.
Here are 10 reasons every security program needs it.
01
Validate That Your Security Investments Actually Work
Every organization has security tools they've never truly tested against real adversary behavior. The EDR vendor promised ransomware protection, the SIEM vendor promised full visibility, the NDR vendor promised lateral movement detection. Adversary emulation is the only way to verify those claims against the specific techniques targeting your industry. When you emulate a named threat actor's post-access playbook and your EDR misses three of seven techniques, that's not a failure — that's intelligence you can act on before a real adversary exploits the same gap.
02
Identify What Is Working — Not Just What Isn't
There's a misconception that offensive testing only reveals failures. A well-executed adversary emulation campaign shows you exactly which controls fire, which SIEM rules trigger, and where your team responds within acceptable timeframes. Knowing your strengths is as valuable as knowing your gaps — it tells you where to invest more, where to build on what's working, and what to highlight in board reporting. When your SOC catches privilege escalation in under four minutes, that's a data point worth documenting.
03
Measure People, Process, and Technology Together
A penetration test tells you if a vulnerability exists. Adversary emulation tells you if the whole system works. It captures time-to-detect, time-to-respond, and time-to-contain across every phase of the kill chain. Did the technology fire the alert? Did the analyst see it? Did the process escalate it? Did the response playbook contain it? With a platform like SCYTHE, campaigns can be paused, rewound, and replayed — so you can re-run the exact same attack chain after tuning detections and measure the improvement in minutes, not months.
04
Train Defenders with Real-World Adversary Behavior
Your blue team can read every MITRE ATT&CK page and still freeze when a real alert fires at 2 AM. Adversary emulation gives defenders hands-on experience with the exact behaviors they'll face in a real intrusion — not sanitized lab exercises, but realistic attack chains running against their actual production tooling. Analysts learn to recognize anomalous process trees, unusual registry modifications, and suspicious lateral movement patterns through practice, not theory. It's a fire drill that uses real fire.
05
Compress Response Time from Days to Minutes
Response time is a muscle. The more your team exercises it, the faster it gets. Organizations that run adversary emulation campaigns regularly — monthly or quarterly rather than annually — see measurable compression in detection-to-containment timelines. The ability to replay the same campaign after each improvement cycle creates a feedback loop that accelerates maturity faster than any other approach. Your first run takes 45 minutes to detect. After tuning, the same campaign triggers an alert in under 3 minutes. That's quantifiable improvement the board can see.
06
Stay Ahead of AI-Accelerated Threats
Adversaries are using AI to generate polymorphic payloads, automate reconnaissance, craft convincing social engineering at scale, and adapt attack chains in real time. The threat landscape is evolving weekly, not quarterly. Static, annual penetration tests can't keep pace. Continuous adversary emulation — building and deploying new campaigns within hours of a CISA advisory or threat intelligence update — is the only way to validate defenses at the speed threats evolve. Platforms with AI-assisted campaign building make this practical even for lean teams.
07
Answer the Board's Hardest Question
Every CISO faces the same question from leadership: "Would that attack be successful here?" When the next headline-making breach or ransomware campaign hits, the board wants an answer backed by evidence — not confidence. Adversary emulation gives you the data to answer with specificity: "We emulated that threat actor's full kill chain last month. Our EDR detected 5 of 7 post-access techniques. We've tuned the remaining 2 and re-validated. Here's the report." That's the difference between an opinion and a defensible position.
08
Right-Size Your DFIR Retainers and External Resources
Most organizations maintain DFIR retainers they've never tested. Adversary emulation lets you measure how quickly your external partners can onboard during a simulated incident, whether your internal team can contain a breach without escalation, and where the handoff gaps exist. This data lets you allocate budget accurately — investing in retainer hours where you actually need coverage rather than guessing based on worst-case assumptions. Some organizations discover they need less external support than they're paying for; others find critical gaps before a real incident exposes them.
09
Meet Regulatory and Framework Requirements
Threat-led penetration testing and adversary emulation requirements are expanding globally. TIBER-EU, CBEST, DORA, TSA SD-02C for critical infrastructure, and evolving NIST and SEC frameworks now expect or require continuous validation of security controls against realistic threat scenarios. Gartner's CTEM framework positions Adversarial Exposure Validation (AEV) as the mechanism for Phase 4 — validating that exposures identified in earlier phases are actually exploitable and that controls actually work. Organizations that already run adversary emulation programs are compliance-ready by default, not by scramble.
10
Build a Purple Team Culture That Compounds Over Time
The deepest benefit of adversary emulation isn't any single test result — it's the culture it creates. When red and blue teams share a platform, run collaborative exercises, and iterate on detection rules together, the adversarial relationship between them transforms into a partnership. Red teamers stop hoarding findings for a dramatic report. Blue teamers stop viewing offensive testing as a gotcha. Junior team members learn adversary tradecraft through hands-on practice. The entire program compounds: each exercise makes the next one faster, more targeted, and more valuable. Over 18–24 months, organizations that invest in this cycle move from reactive compliance to genuine offensive maturity.
The Only Way to Know Is to Test
A breach doesn't have to mean business impact. Organizations that emulate real adversary behavior — continuously, against their production environment, measuring people, process, and technology together — build the resilience to detect intrusions early, contain them quickly, and recover before the damage is done.
You can't know if your defenses work by reading a vendor datasheet, passing an audit checkbox, or reviewing last year's penetration test. You know by emulating the adversaries targeting your industry, running their post-access playbook against your stack, and measuring what happens. Everything else is assumption.
Replace Assumptions with Evidence
See What Your Defenses Actually Catch
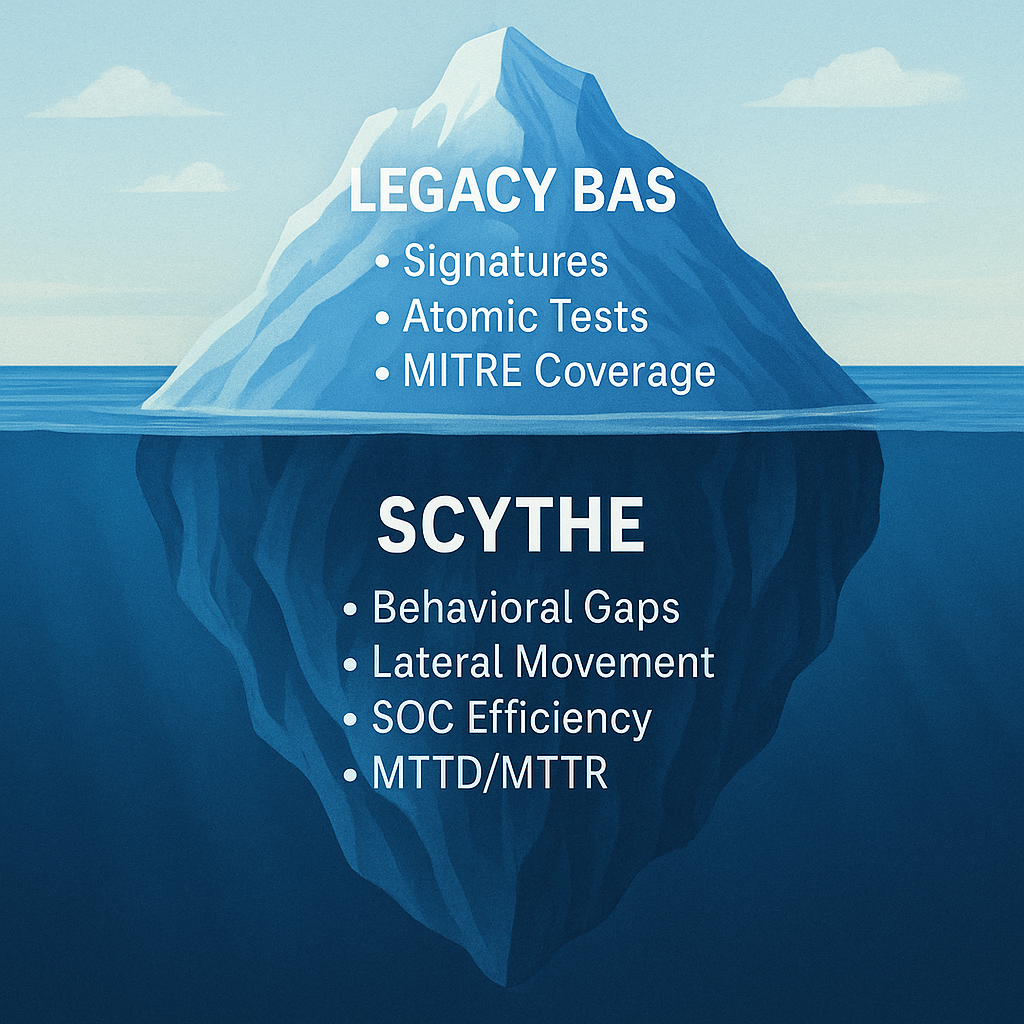
SCYTHE gives red, blue, and purple teams a single platform for continuous adversary emulation — with 1,400+ pre-built campaigns mapped to MITRE ATT&CK, AI-assisted campaign generation, and the ability to pause, rewind, and replay attack chains to measure improvement. Go from threat advisory to validated detection in hours.
Learn where you stand: Download the Offensive Cybersecurity Maturity Roadmap
Schedule a Demo
.png)

.png)

