Opinion Controls Validation Red Teaming Purple Teaming
Simulation tools test what's already known. Adversary emulation validates whether your defenses work against how real threat actors actually operate — and that distinction is the difference between compliance and security.
SCYTHE · Updated April 2026 · 8 min read
Threat actors don't follow scripts. They adapt, improvise, and chain techniques together in ways no predefined playbook anticipates. Yet most organizations still rely on simulation tools that test their defenses against fixed, known attack paths — and call it validation.
The gap between cybersecurity simulation and adversary emulation isn't academic. It's the difference between knowing your firewall rules exist and knowing whether your entire security stack — EDR, SIEM, SOC analysts, IR runbooks — can detect and respond to the TTPs that real adversaries are using right now. In 2026, with AI accelerating the threat landscape and Gartner's CTEM framework driving security strategy, understanding this distinction is more critical than ever.
What Is Cybersecurity Simulation?
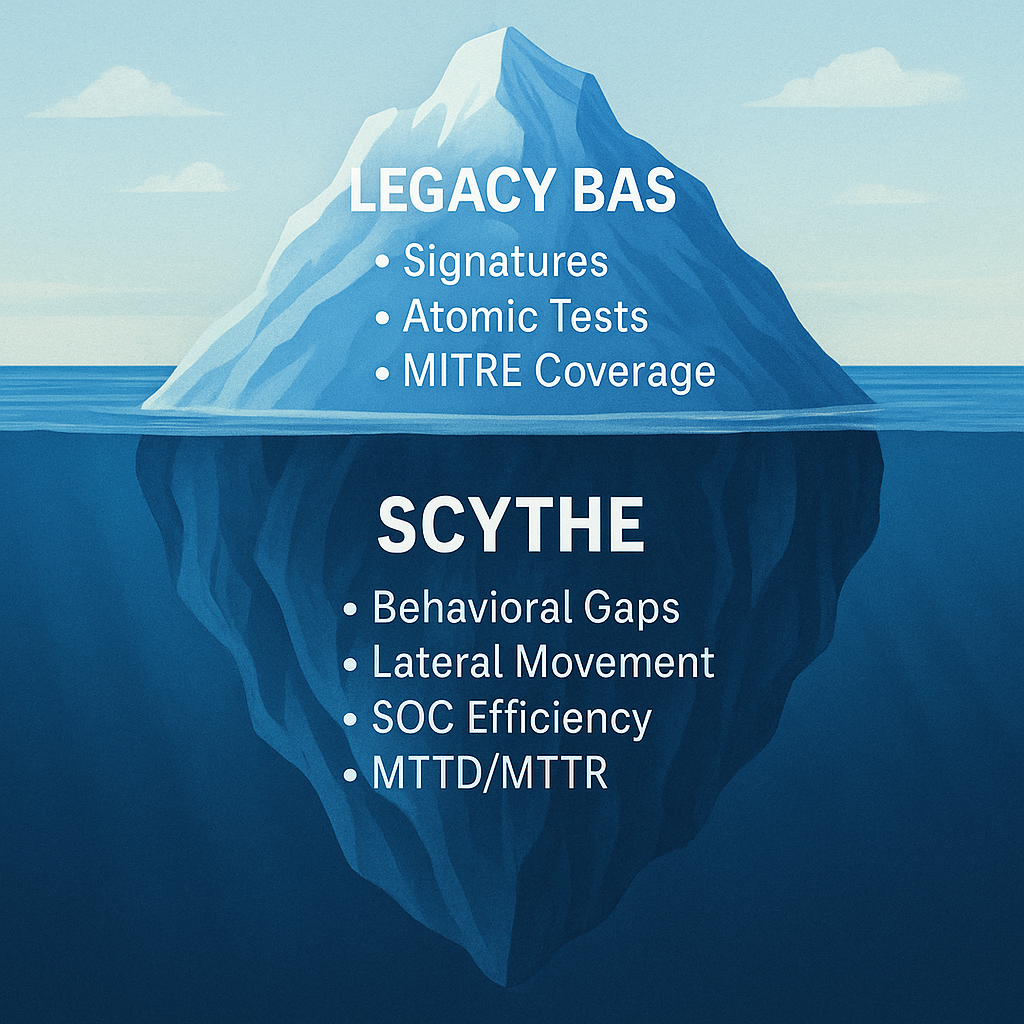
Breach and Attack Simulation (BAS) tools use predefined, automated attack paths to test whether specific security controls trigger as expected. They follow a scripted methodology: execute known technique A, check if control B fires, log the result. The attack path is fixed. The sequence doesn't change. The tool runs the same test the same way every time.
This approach has its place. It's useful for basic control validation — confirming that a SIEM rule still fires after a configuration change, or that an EDR policy hasn't been accidentally disabled. But simulation only tests the technology layer, and only against known patterns.
The Problem
Simulation tools test what you already know should be detected. They don't test what happens when an adversary pivots, chains techniques in unexpected order, or uses legitimate tools to evade the controls you've deployed. They validate configuration. They don't validate readiness.
The limitations compound at scale. Legacy BAS tools are often rigid — organizations must wait for the vendor to update the attack library when new TTPs emerge. Many require advanced scripting skills to customize. And critically, they test technology in isolation, ignoring the people and process dimensions that determine whether a real incident is contained or becomes a breach.
What Is Adversary Emulation?
Adversary emulation replicates how real threat actors actually behave — not just the techniques they use, but the way they chain them together, adapt to defenses, and pursue objectives through multi-stage campaigns. It uses the same modular tactics, techniques, and procedures (TTPs) mapped to MITRE ATT&CK that threat actors deploy in the wild, executed against your production environment.
Where simulation asks "does control X fire when it sees technique Y," emulation asks a fundamentally different question: if a named threat actor targeted your organization today, would your people detect the intrusion, would your processes contain it, and would your technology stop it before impact?
This is what Gartner now calls Adversarial Exposure Validation (AEV) — the validation phase within the Continuous Threat Exposure Management (CTEM) framework. It's the evolution beyond BAS, and it's where the industry is heading.
| |
Simulation (Legacy BAS) |
Adversary Emulation (AEV) |
| Attack paths |
Predefined, fixed |
Modular, customizable, threat-informed |
| What it tests |
Individual controls (technology only) |
People, process, and technology together |
| MITRE ATT&CK |
Partial coverage |
Full kill-chain mapped to named threat actors |
| Adaptability |
Wait for vendor updates |
Build and deploy new campaigns in hours |
| Skills required |
Often requires advanced scripting |
Intuitive interface, drag-and-drop, AI-assisted |
| Team collaboration |
Red team only |
Red, blue, and purple team workflows |
| Cadence |
Periodic, scheduled |
Continuous, event-triggered, and scheduled |
| Output |
Pass/fail on known controls |
Validated detection posture with remediation priorities |
Why the Distinction Matters More in 2026
Three forces have made the simulation-vs-emulation gap more consequential than ever:
AI-accelerated threats. Adversaries are using AI to generate polymorphic payloads, automate reconnaissance, and adapt attack chains in real time. Fixed simulation paths can't keep pace with threats that evolve weekly. Emulation platforms that let you build and deploy new campaigns within hours of a new threat advisory can.
CTEM adoption. Gartner's Continuous Threat Exposure Management framework has moved from trend to operational reality. The validation phase (Phase 4) explicitly requires testing that controls work against real-world threats — not just confirming that rules exist. Simulation tools validate configuration. Emulation validates exposure.
The skills gap persists. Security teams are smaller than they should be, and the complexity of the threat landscape is growing faster than headcount. Organizations need tools that democratize offensive testing — letting blue team members create emulations, junior red teamers build campaigns through an intuitive interface, and purple teams collaborate in a shared environment without requiring everyone to be a coder.
What to Look for in an Adversary Emulation Platform
If your organization is evaluating whether to move beyond legacy BAS or invest in adversary emulation for the first time, here's what matters:
Full kill-chain campaign execution. The platform should let you build multi-stage attack campaigns that mirror how real adversaries operate — from initial access through lateral movement to objective completion — not just test individual techniques in isolation.
A continuously updated threat library. Pre-built campaigns mapped to named threat actors and MITRE ATT&CK, updated as new advisories drop. You shouldn't have to wait for a vendor release cycle to test against last week's CISA alert.
AI-assisted campaign building. Describe your test objective in plain language, and the platform generates a realistic, multi-stage attack path aligned to your threat landscape and target controls. This closes the skills gap and accelerates time-to-emulation.
Cross-platform coverage. Windows, macOS, Linux, cloud-native, and OT/ICS environments from a single platform. Your attack surface isn't single-OS; your emulation platform shouldn't be either.
Purple team collaboration built in. Red, blue, and purple teams should be able to work in a shared environment — with bi-directional reporting, shared campaign visibility, and results that tie directly into SIEM, EDR, and ITSM workflows.
Continuous and event-triggered execution. Emulation should run on a schedule, trigger automatically when your environment changes, and produce results that feed into a continuous improvement loop — not a one-off report that sits in a drawer.
Emulation Makes Purple Teaming Real
The original post made an important point that's even more relevant today: cybersecurity is a team sport. Red teams are competitive and creative. Blue teams are methodical and defensive. The tension between them can produce friction — or, with the right platform, collaboration that makes both sides stronger.
Adversary emulation is what makes purple teaming operationally real. When both teams share a platform — where red can build and execute campaigns, blue can see results in real time, and both can iterate on detection rules together — the exercise produces outcomes that neither team could achieve alone.
Blue team members don't need to become red teamers. But they do need the ability to create emulations that test their own detections — and the platform should make that possible without requiring coding skills. Junior red team members need a way to build campaigns using modular TTPs and an intuitive interface, learning adversary tradecraft through hands-on practice rather than classroom theory.
The true adversaries are out in the wild. The people inside your organization are allies — and the right emulation platform makes that collaboration effortless.
Move Beyond Simulation
SCYTHE: Adversary Emulation That Validates People, Process, and Technology
SCYTHE's AEV platform gives red, blue, and purple teams the ability to emulate real-world adversaries, validate detection and response across the full kill chain, and produce the evidence-based results that drive continuous improvement. With 1,400+ pre-built threat campaigns, AI-assisted campaign generation, and native integrations with your SIEM, EDR, and ITSM stack — your team can go from threat advisory to validated detection in hours, not weeks.
Schedule a Demo

.png)
.png)